A team of researchers, including experts involved in the discovery of the Meltdown and Spectre vulnerabilities, have disclosed a new type of side-channel attack that targets the operating system page cache.
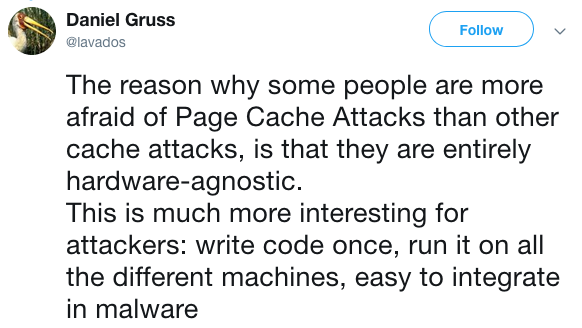
Unlike Meltdown, Spectre and other side-channel attack methods disclosed in the past year – these were possible due to design flaws in microprocessors – page cache attacks are hardware agnostic and they have been demonstrated to work against both Windows and Linux systems.
Page caches are software caches containing all the memory pages associated with files and applications. Page caches give the operating system quicker access to data and reduce the number of disk reads, thus improving performance.
A group of researchers from the Graz University of Technology, Boston University, NetApp, CrowdStrike and Intel have shown how these page caches can be abused for both local and remote attacks.
They demonstrated that an unprivileged piece of malware running on the targeted system can leverage the page cache for various types of activities. Attackers can create a high-speed covert channel that bypasses a sandbox, they can place phishing windows on top of a legitimate application, they can log keystrokes, and reconstruct temporary passwords generated by frameworks that use the current UNIX timestamp for pseudo-random number generation.
Remote page cache attacks are also possible, but they are not hardware agnostic. The remote version of the attack can be used to create a covert channel for exfiltrating information over the network from a protected system using innocuous server request.
While attacks have been successfully conducted by the researchers against both Windows and Linux systems, they pointed out that the method is much more efficient on Windows than it is on Linux.
Michael Schwarz, one of the researchers representing the Graz University of Technology, told SecurityWeek that they have not tested the attack against Apple’s macOS operating system.
The researchers noted that the impact of page cache attacks is not as big as in the case of Meltdown and Spectre. However, they have reported their findings to Microsoft and Linux developers, and they are already said to be working on mitigations. In their paper on page cache attacks, the experts have proposed a series of countermeasures that operating system vendors can implement to mitigate these types of attacks.
Related: Researchers Disclose 7 New Meltdown, Spectre Attacks
Related: Tech Firms Coordinate Disclosure of New Meltdown, Spectre Flaws
Related: Remote Spectre Attack Allows Data Theft Over Network












