VirusTotal on Wednesday announced that its malware scanning engine now supports firmware images, characterizing them as legit or malicious.
Just as any application, firmware is prone to vulnerabilities and different types of malware, and can also be targeted for surveillance purposes, something that NSA was revealed to have attempted several years ago.
As VirusTotal’s Francisco Santos explains in a blog post, one of the most targeted firmware is BIOS, which allows cybercriminals to load code before the boot process. Furthermore, malware deployed in firmware can survive reboots, system wiping and reinstallations, and avoids antivirus scanning, which leads to persistent compromise.
The newly added capability in VirusTotal was designed with support for tasks such as Apple Mac BIOS detection and reporting; strings-based brand heuristic detection, to identify target systems; extraction of certificates both from the firmware image and from executable files contained in it; PCI class code enumeration, allowing device class identification; and ACPI tables tags extraction.
Moreover, it offers NVAR variable names enumeration; option ROM extraction, entry point decompilation and PCI feature listing; extraction of BIOS Portable Executables and identification of potential Windows Executables contained within the image; and SMBIOS characteristics reporting.
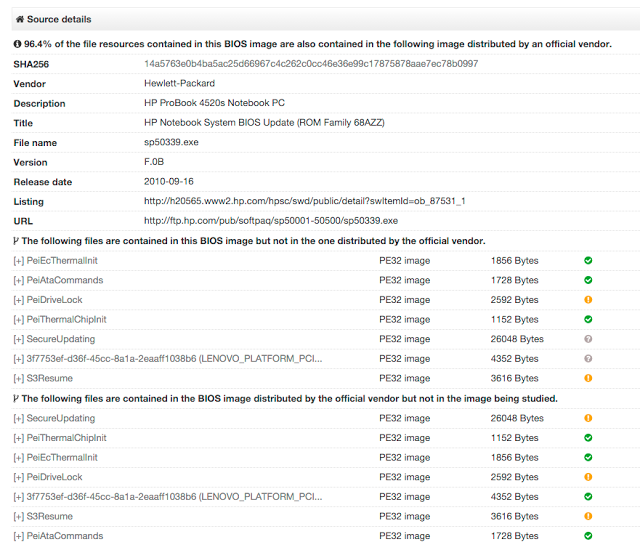
Users can now take advantage of extraction of the UEFI Portable Executables that make up the image, which represents the code usually used for infection, Google-owned VirusTotal says. These executables are extracted and submitted individually, allowing users to view a report for each one of them, and the tool also highlights which of these PEs are Windows targeted, since the layer can also include Windows executables.
Users can view details on the firmware they have submitted for scanning by clicking on the Additional information tab, which also has a new Source Details field. The File Detail tab will also provide various details on the characteristics of the submitted firmware image.
There are various tools that users can take advantage of when looking to dump their system’s BIOS in order to submit it for analysis. However, VirusTotal notes that, should the BIOS be compromised in such a manner that dumpers are deceived, users are advised to physically attach to the chip and electronically dump the flash memory.
Users are also advised to remove any private information from BIOS dumps before uploading them to VirusTotal, especially since vendors might store details such as WiFi passwords in BIOS variables. Mac users, for example, can use DarwinDumper to strip sensitive information from BIOS by checking the “Make dumps private” option.
VirusTotal also notes that Teddy Reed, developer of the UEFI firmware python parser, had an important role in the addition of support for firmware images to the service.
Related: Researchers Find Several UEFI Vulnerabilities
Related: EFI Zero-Day Exposes Macs to Rootkit Attacks: Researcher
















