A Dutch engineer recruited by the country’s intelligence services may have used a water pump to deploy the now-infamous Stuxnet malware in an Iranian nuclear facility, according to a two-year investigation conducted by Dutch newspaper De Volkskrant.
Stuxnet, whose existence came to light in 2010, is widely believed to be the work of the United States and Israel, its goal being to sabotage Iran’s nuclear program by compromising industrial control systems (ICS) associated with nuclear centrifuges. The malware, which had worm capabilities, is said to have infected hundreds of thousands of devices and caused physical damage to hundreds of machines.
De Volkskrant’s investigation, which involved interviews with dozens of people, found that the AIVD, the general intelligence and security service of the Netherlands, the Dutch equivalent of the CIA, recruited Erik van Sabben, a then 36-year-old Dutch national working at a heavy transport company in Dubai.
Van Sabben was allegedly recruited in 2005 — a couple of years before the Stuxnet malware was triggered — after American and Israeli intelligence agencies asked their Dutch counterpart for help. However, the Dutch agency reportedly did not inform its country’s government and it was not aware of the full extent of the operation.
Van Sabben was described as perfect for the job as he had a technical background, he was doing business in Iran and was married to an Iranian woman.
According to one of De Volkskrant’s sources, the Stuxnet malware was planted on a water pump that the Dutch national installed in the nuclear complex in Natanz, which he had infiltrated. The malware would allegedly be able to spread on the network once the pump was connected to the system.
It’s unclear if Van Sabben knew exactly what he was doing, but his family said he appeared to have panicked at around the time of the Stuxnet attack.
It was previously reported that Dutch intelligence had recruited an Iranian engineer to plant Stuxnet.
Van Sabben passed away in the United Arab Emirates two weeks after the Stuxnet attack as a result of a motorcycle accident.
Michael Hayden, who at the time was the chief of the CIA, did agree to talk to De Volkskrant, but could not confirm whether Stuxnet was indeed delivered via water pumps due to it still being classified information.
It was previously reported that Stuxnet was planted using a USB flash drive and it’s unclear if either or both methods were actually used to deliver the malware.
Ralph Langner, a researcher who conducted an in-depth analysis of Stuxnet after the malware’s existence came to light, noted that “a water pump cannot carry a copy of Stuxnet”.
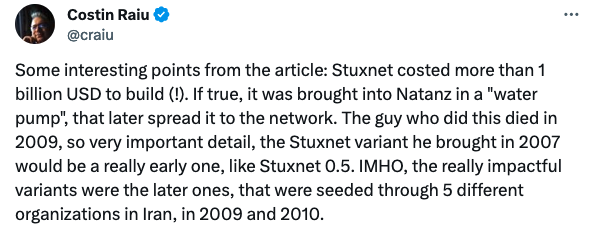
One interesting piece of information that has come to light in De Volkskrant’s investigation is that Hayden reportedly told one of the newspaper’s sources that it cost between $1 and $2 billion to develop Stuxnet.
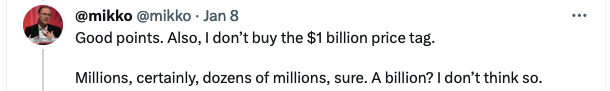
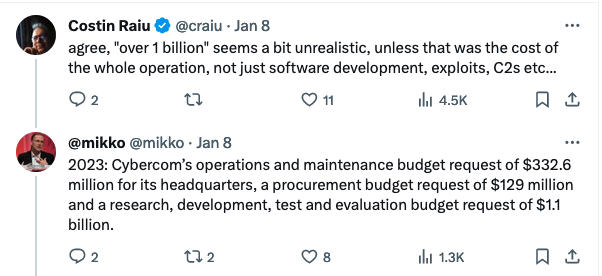
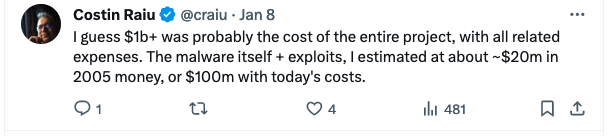
Costin Raiu, a reputable member of the cybersecurity industry and former director of Kaspersky’s research team, and Mikko Hypponen, chief research officer at WithSecure, have expressed some doubts regarding the amount.
Raiu has also made some comments on which version of Stuxnet may have been deployed by Van Sabben based on the claims in the Dutch newspaper.
*article updated with comments from Raiu, Hypponen and Langner
*updated on January 16 with information from previous reports about a USB flash drive being used to deliver Stuxnet
Related: New Vulnerabilities Allow Stuxnet-Style Attacks Against Rockwell PLCs
Related: Suspected Cyberattack Paralyzes the Majority of Gas Stations Across Iran


