When using cyber threat intelligence to track cyber criminal activity and impact, it’s clear that the bad guys follow the path of least resistance and most profit. This is why I wrote about cyber threats not generally being as complex as they’re made out to be. While malicious actors demanding ransoms is not new, the surge of organizations being targeted with fake extortion demands and empty threats is.
Ransomware gathers so many headlines these days and cyber criminals know they can exploit the fear of an unprepared organization being told that their data has been stolen/encrypted. As ransomware campaigns have ramped up, so too have extortion efforts. Let’s look at how extortion campaigns are carried out through the “avenue of approach” lens.
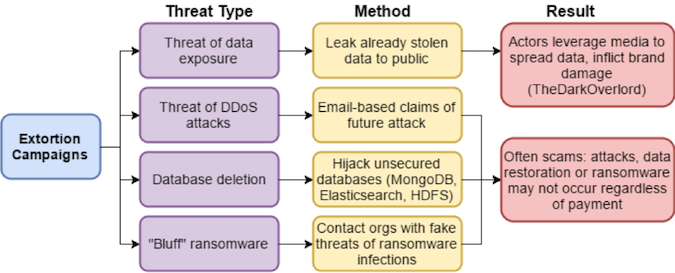
Walking through the extortion threat types, we can examine what you should and should not do:
Threat of data exposure: This type of extortion has been used over the past year by an actor known as TheDarkOverlord which has been breaching organizations, stealing data and attempting to blackmail those those organizations with the threat of leaking data since the summer of 2016. TheDarkOverlord and similar actors frequently leak stolen data to the media, leveraging them in several ways. For starters, the organizations that do not pay the ransom have their names tarnished as their data is spread through traditional reporting. Perhaps the more important angle, however, is the way in which the TheDarkOverlord is able to use the media to create legitimacy as an extortionist and encourage future victims to pay the blackmail.
When it comes to extortion, planning is a key component to reducing your risk of being a victim. Incident and breach response teams typically practice test runs of various scenarios to ensure the plan is sound and will be well-executed in the event that disaster strikes. Knowing your adversaries can greatly help when it comes to this pre-planning. Be sure you can answer questions such as:
· What groups would target your business and why
· What are they targeting?
· What is their intent?
· What are their capabilities?
· What opportunities are you presenting?
· What are the possible attack scenarios?
Threat of DDoS attack: Paying an extortionist is not a good idea, but if you plan to do so, at the very least, confirm that the attacker has the capability (Has the adversary successfully carried out this attack previously?) and opportunity (i.e. What is your level of presence? Are you exposed?) to follow through with a DDoS threat. There has been a rise in extortion bluffs, or fake extortion attempts, where a DDoS is threatened in advance via email. Little effort is required to make such a threat with much to gain if not vetted. From a preventative perspective, look at your infrastructure and figure out your level of risk of being hit with a DDoS attack. How easy would it be to take your business offline? What plan B do you have in place?
Database deletion: Before even considering paying an extortionist (which I would not recommend), confirm that the attacker is actually in possession of the data and has the ability to restore it before payment. Cyber criminals are actively competing with each other to delete the databases and post the most up-to-date ransom demand – regardless of if the extortionists possess the original data and even have the ability to restore it. Looking at this issue more proactively, database extortion attempts exploit poor database authentication and encryption and poor backup processes. Regular backups are the best option to mitigate the risk of data loss, and properly securing any Internet-connected database is the best way to avoid this type of data theft. Of the 125 “victims aided” in the recent MongoDB hijacking attacks, only 14 reported having a recent backup from which they could restore the deleted data. That means roughly 90% of the victims were both using improper authentication on Internet-accessible databases and did not take the step of properly backing up that exposed data.
“Bluff” ransomware”: Successful extortion efforts have spawned campaigns that go beyond the time-consuming task of actually carrying out a cyber-attack and instead rely purely on extortion via fake threats. This type of campaign is where malicious actors contact organizations to demand a ransom and lie about the organization’s data being encrypted. In fact, more than 40 percent of 500 IT decision makers at large UK businesses surveyed in November 2016 said they had been contacted by cyber criminals claiming a ransomware infection, and two-thirds of those contacted reportedly paid the ransom demands despite it only being a “bluff.” While it’s best practice NOT to pay a ransom, if you’re going to do so, you should require that the malicious actor shows proof that they can do what they are threatening. Otherwise you’ll just end up fanning that flame.
The explosion of ransomware over the past few years has pushed cyber-extortion into the mainstream, and malicious actors are capitalizing on that growing concern with a variety of extortion-related threats that play off those fears. In addition, the growth of digital currencies such as Bitcoin, which easily allow anonymous payments to cybercriminals, has made it easier than ever for bad actors to extort organizations with little fear of being caught. These trends suggest that we may be in the beginning of a golden age of cyber-extortion.
However, extortion campaigns are generally made profitable by numerous victims making relatively small payments, and that requires using wide-reaching tactics, most of which are well known. The wide-open databases, empty threats of ransomware and other extortion attempts can be largely defended against with basic security precautions, regular backups and a healthy dose of cyber threat intelligence to help point organizational resources in the proper direction.
















