Cyber threat intelligence means different things to different people and as such I’ve spent the last several articles exploring a threat intelligence mind map and the different levels of threat intelligence:
• Strategic cyber threat intelligence
• Operational threat intelligence
• Tactical threat intelligence
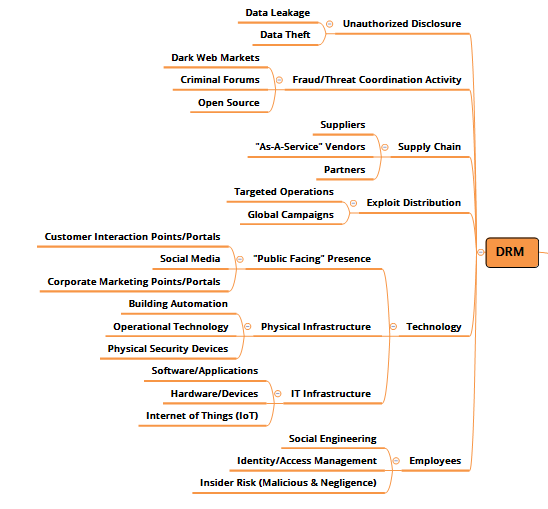
Next up, I’d like to examine the concept of Digital Risk Monitoring (DRM) – also known as Digital Risk Management – and how this fits into your overall threat intelligence program.
When thinking about cyber threats, it is important to keep in mind that malicious actors are going to favor targets of opportunity that are weak or soft … or in other words the opportunities you are presenting to them. A growing part of a threat intelligence capability isn’t just looking at the threats attacking you from a traditional IT Security perspective and how other others in your industry are being hit, but also correlating threats with the risks within your digital ecosystem.
By including digital risk monitoring as part of your threat intelligence capability, you can better understand your most critical areas of risk and the possible avenues of approach for adversaries, how actor capabilities align with the opportunities you’re giving them and how to stay ahead of them. Let me further define what I mean by risk… I don’t JUST mean the information security risk, but also the business risk. For example here are just a few quick questions to ask yourself:
• Are malicious actors talking about your company/brand in social media or dark web forums?
• What’s the impact of a cyber threat on your brand and reputation?
• What risks are the third parties with whom you conduct business providing to adversaries as an opening into your organization?
• What risks to your organization are associated by employee use of IoT devices?
Conceptually all of this makes a lot of sense, but actually having visibility of and understanding where your risks are and the level of criticality of each risk is no easy task. And not to be a fear monger, but as businesses and users increase their interconnectedness and interactivity, that digital risk footprint grows. In the DRM section of the mind-map I created, I’ve broken out different areas of digital risk, what I refer to often as the opportunities you’re presenting.
• Your employees, aka insiders, constitute a major risk area either through malicious activity (stealing sensitive customer/company information), through negligence, or through active targeting by malicious actors. This typically can come in the form of placing a file(s) in an unauthorized location, falling victim to a social engineering technique and giving up account information or being a bit too quick in sharing information with third parties. Bottom line is it is important to monitor when instances such as these pop up outside of your infrastructure.
• Your technology is another key risk area and this is a big one simply because there is so much to cover. Not only do threats target vulnerabilities in traditional IT environments, but now with IoT devices becoming commonplace (I just read something about a “smart” fish tank leaving a casino vulnerable!) both from a user and a building automation perspective, the technology footprint has very quickly grown exponentially. This is further exacerbated by your organization’s own public-facing infrastructure. It used to be a website, but now it’s all of your social media channels, your chat functions, your customer and partner portals. There is a lot to get a handle on here.
• Exploit distribution – What exploits are out there that effect your organization? Do you know? Do you have plans to address the impact of these if used against you? Much like leaked personal data, once those vulnerabilities, exploits, and tools are exposed, they forever remain in the cybercriminal public domain. The impact of that type of information being leaked can spread further, wider, and be more long-lasting than perhaps any other type of cyber incident.
• Your supply chain is an extension of your business and as such needs to be brought under some sort of visibility and management from a digital risk perspective. Everyone knows about the Target breach from a few years back and it’s the perfect use case of understanding the risk you have based on your third party vendors. Supply chains get messy because it’s not just your immediate vendors, but their vendors as well. That supply chain can explode, so there are limits to what makes sense, but it’s pretty clear that having a view of supply chain cyber risks is a key component of your overall intel effort.
• Fraud and threat coordination activity has to do with the bad guys. In dark web markets and cybercriminal forums, they talk amongst each other and conduct business in similar fashion to how legitimate business is conducted. Malicious actors do recon against you and share information regularly with each other. Having visibility of these conversations, what is for sale, what is actively being targeted is a critical source of intel you can use to minimize your exposure and to better plan out your defense.
Understanding your digital risk is a key ingredient to the mix when crafting or adding to a threat intelligence program. In many instances DRM is being treated as a separate capability area apart from CTI and therefore tends to be “out of sight, out of mind” for many organizations which is unfortunate as it should be a core component of your CTI program. The bottom line here is that DRM is a component of CTI for the following reasons:
1. It is collecting data on risks and threats to your organization
2. It is informing decision makers as to their “level of presence” wi
thin the digital realm
3. When data is collected it is evaluated for impact to the organization
4. You can derive “Course of Action” from the effort and seek to change outcomes
5. You can understand what actor motivations and intentions are as it directly relates to your organization
Whether you like it or not, your organization has some kind of “Level of Presence” out there that requires continuous monitoring. The better you understand that presence, the better you prepared you are to mitigate risk. If you don’t have DRM identified as a component of your CTI program, you should.

