As technology advances continue across industry we can automate more and more tasks. As it relates to intelligence work, automation can play an important role, but it is not a solution unto itself. As we’ve walked through the cyber threat intelligence mind map, we’ve examined different functional areas/capabilities including Strategic, Operational and Tactical threat intelligence as well as digital risk monitoring, and in the last article we explored the importance that process plays. In our final section of the mind map, we take a look at another glue-like component of a threat intelligence program – people.
Intel is created, communicated and consumed by people. Automation can help significantly cut down on manual efforts around data collection and evaluation, filter out white noise, and speed the intel process. But at the end of the day, you need people involved who can analyze intel, report critical findings to key stakeholders and then have those decision-makers be able to quickly take best courses of action to mitigate threats.
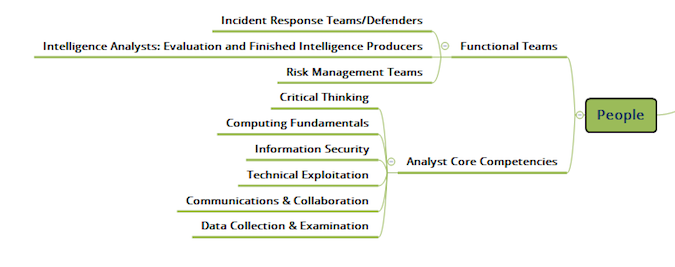
The below graphic is the zoomed in version of the “People” section of the mind map. I’ve broken this out into core competencies that intel analysts should have (at least these are what I look for when hiring for my team) and then the primary functional teams that are involved in cyber threat intelligence.
When it comes to a threat intelligence analyst, there are many skills needed and many focus areas that can be weighted differently depending on the organization and how you’re structured. Analysts can focus on different areas based on their expertise since it’s such a wide range of information that must be collected, processed and analyzed. Ultimately, intelligence needs to be distilled down into something “usable”. Many people use the term “actionable” but to be honest I prefer to make intelligence “usable”, which is defined by the organization receiving it.
Defining what is usable (i.e. the mission) for the analyst team as well as for individual analysts is critical so that their time and energy is focused on the right things. For example, a defender or forensic analyst utilizing intel to analyze malware would unlikely be the same person who is developing a risk-based actor profile operating in a particular industry. Additionally, that same analyst may/may not provide a finished report and present to necessary stakeholders.
The point here is that a threat intel analyst wears many many different hats and must be able to understand both the technical side of security, be able to navigate underground forums and markets on the dark web, understand the business risk aspect, and be able to look at things from under a microscope and from afar to help derive complete context around a potential threat. Communication skills are also a must – especially since breakdowns between operations teams such as IT security groups and the business side are all too common. An analyst must bridge that gap. Automation certainly ain’t gonna do it.
In terms of functional teams – how organizationally people are placed in terms of how to create and consume threat intel – I see three core areas:
1. Incident and/or breach response – this is the traditional use case for intel used by the defender. When an incident or breach occurs, this team kicks into high gear to understand what happened and provide not only some rectification actions, but also mitigation steps for next time around. Responders are not only consumers of intel, but they can also add to the intel process through their own research and recommendations. There should be a continuous loop here as it is definitely NOT a one way street.
2. Intel analysts – these are the folks who analyze volumes of information (that ideally is filtered down through automation) and produce finished intelligence for use throughout the organization. In my experience, the really good analysts have both intel and security expertise because there are multiple potential impacts from a cyber threat. Strategic, risk-based intel can be created and fed to the risk management team and to executives. TTP level analysis and breaking down malware is important to IR teams and to security personnel.
2. Risk management – this is the group/function that takes the cyber threat intelligence and puts it in the context of the overall business, alongside other non-cyber related risk areas. They are likely taking a non-technical approach in order to give decision makers a pure risk posture for the organization.
I have seen plenty of organizations staff their analyst teams with plenty of people who could code in their sleep and can reverse engineer all kinds of crazy things at the drop of a hat and more power to them. What I don’t see a lot of organizations doing however, is first defining what is “usable” for them to consume and then staffing t
o that need. Many organizations think they know what they need without really going down the path to defining it and then staff based off of that assumption.
Want to hire the best analyst? Then first define what is usable and then focus your search on those characteristics.

