The Zero Day Initiative (ZDI) on Monday announced the targets and prizes for the next Pwn2Own Miami hacking contest, which focuses on industrial control system (ICS) products and associated protocols.
Pwn2Own Miami 2022 is scheduled to take place on January 25-27, 2022, and it has four main target categories: control server, OPC UA server, data gateway, and human-machine interface (HMI).
In the control server category, participants can earn up to $20,000 for hacking Iconics Genesis64 and Inductive Automation Ignition products.
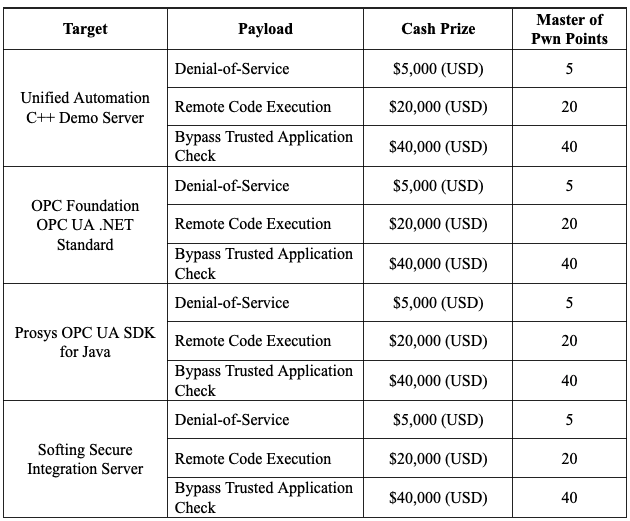
In the OPC UA category, white hat hackers can earn between $5,000 and $40,000 for demonstrating exploits against the Unified Automation C++ demo server, the OPC Foundation’s OPC UA .NET standard, the Prosys OPC UA SDK for Java, and Softing Secure Integration Server. The highest rewards are for security bypass exploits and the lowest rewards are for DoS vulnerabilities.
In the data gateway category, researchers can get a prize of up to $20,000 for arbitrary code execution exploits affecting the Triangle Microworks SCADA Data Gateway product or the Kepware KEPServerEx server.
The same maximum prize is offered in the HMI category, where participants are expected to demonstrate code execution on AVEVA Edge and Schneider Electric EcoStruxure Operator Terminal Expert products.
The deadline for signing up is January 21, 2022. Researchers have to submit a paper detailing their exploits and how they can be executed.
Pwn2Own Miami 2022 is expected to be a hybrid event, with contestants invited to attend physically from the S4 conference in Miami and remotely from anywhere in the world. However, ZDI noted that remote participants will not be able to modify their exploits during their attempt if something goes wrong.
At last year’s event, participants earned a total of $280,000 for demonstrating 24 vulnerabilities against products from Rockwell Automation, Schneider Electric, Triangle MicroWorks, Unified Automation, Iconics, and Inductive Automation.
Related: $1.9 Million Paid Out for Exploits at China’s Tianfu Cup Hacking Contest
Related: Pwn2Own 2021 Participants Earn Over $1.2 Million for Their Exploits
Related: $200,000 Awarded for Zero-Click Zoom Exploit at Pwn2Own















