iOS 15, Chrome, Windows, VMware Hacked at China’s Tianfu Cup
Several white hat hacker teams that took part in the Chinese hacking contest Tianfu Cup over the weekend earned hundreds of thousands of dollars for their exploits.
The Tianfu Cup hacking competition is similar to Pwn2Own — participants can earn significant rewards for vulnerabilities and exploit chains targeting widely used software and hardware. The event has been taking place in Chengdu, China, and, in the past years, participants have earned a total of $1 million (2018), $500,000 (2019) and $1.2 million (2020).
At the latest edition, participants demonstrated exploits targeting Windows 10, Ubuntu, iOS 15 on iPhone 13 Pro, Microsoft Exchange, Chrome, Safari, Adobe Reader, Parallels Desktop, QEMU, Docker, VMware ESXi and Workstation, and ASUS routers. Only Synology products were not hacked at this year’s event.
Participants earned a total of roughly $1.9 million, with the first three teams taking home $654,500, $522,500 and $392,500.
The biggest single reward, $300,000, was earned by Team Pangu for a remote jailbreak targeting the iPhone 13 Pro with iOS 15. The exploit was triggered with a single click on a specially crafted link.
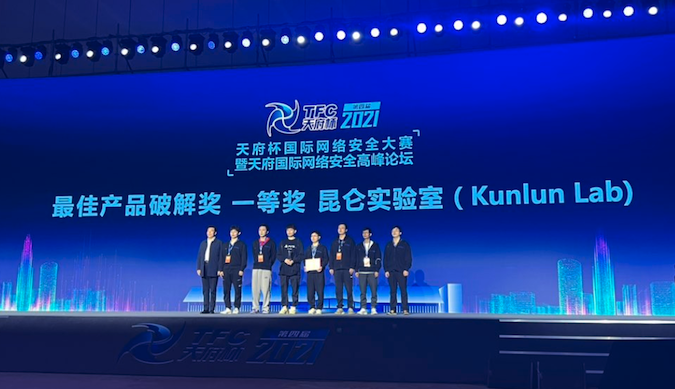
The winning team, which represented Chinese cybersecurity company Cyber Kunlun, successfully demonstrated exploits targeting Chrome, Adobe Reader, VMware ESXi and Workstation, the iPhone 13 Pro, Safari on macOS, and Windows 10.
The Kunlun team managed to achieve remote code execution on iOS 15, even though the company’s researchers helped Apple patch a race condition in previous versions of the operating system that could have been exploited to execute arbitrary code with kernel privileges.
A law that came into effect in September in China requires citizens who find zero-day vulnerabilities to pass the details to the government. They cannot sell or give the information to any third-party outside of China, except from the vulnerable product’s manufacturer.
Related: VMware Patches ESXi Vulnerability That Earned Hacker $200,000
Related: VMware Patches Vulnerabilities Exploited at Chinese Hacking Contest
Related: China May Delay Vulnerability Disclosures For Use in Attacks














