An Iranian cybersecurity firm claims to have discovered a sophisticated rootkit that is designed to target HP servers.
The malware, dubbed iLOBleed, was analyzed by Tehran-based Amnpardaz, which indicates that it has been used to target organizations in Iran. However, no other information has been shared on victims.
It’s unclear who is behind the attacks involving iLOBleed, but its sophistication suggests it’s likely an advanced persistent threat (APT) actor. The United States and Israel are suspected to have launched sophisticated cyberattacks against Iran.
According to Amnpardaz, iLOBleed is an implant that targets HPE’s Integrated Lights-Out (iLO) embedded server management technology, which enables users to remotely monitor, configure and update their servers. iLO is embedded on the motherboard of HP servers.
The rootkit, first spotted in 2020, appears to leverage iLO firmware vulnerabilities discovered and disclosed publicly in the past years. The Iranian company’s researchers noted that while these flaws may be fixed in more recent versions of HP firmware, an attacker can downgrade the firmware to a vulnerable version, which is possible on most systems, except for Gen10 series servers, on which users can enable a non-default setting that prevents firmware downgrades. Users cannot completely disable iLO.
Such rootkits are highly persistent and stealthy, and they can be delivered to targeted devices through the dedicated iLO network port, as well as through the server’s operating system by a user with administrator or root privileges.
“This means that even if the iLO network cable is completely disconnected, there is still the possibility of infection with the malware,” Amnpardaz wrote in a blog post published last week.
Once it has been deployed on a device — the rootkit adds a malicious module to the iLO firmware — iLOBleed gives the attackers full control over the compromised machine.
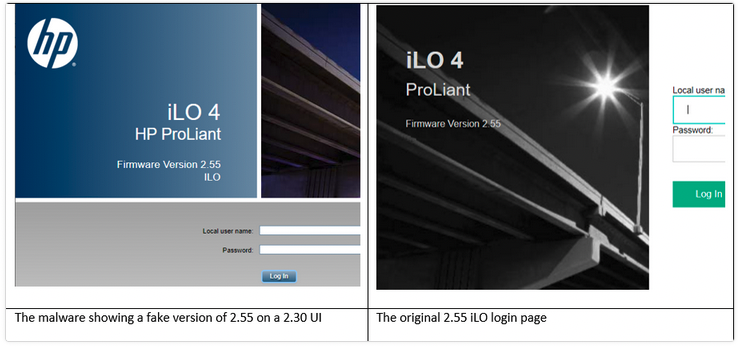
It also silently prevents firmware updates but goes to great lengths to make it look like the update process has been completed successfully to avoid raising suspicion.
“The malware pretends the upgrade to be successful, with all the right messages and logs. Even the exact number of firmware versions is extracted and displayed in appropriate places in the web console and other locations, although in fact no upgrade has been performed,” the researchers explained.
When Amnpardaz discovered the malware, the attackers initiated a process that involved repeatedly wiping the infected server’s disk, likely in an effort to cover their tracks.
Amnpardaz has informed organizations concerned about their servers getting infected with this rootkit that the best way to detect iLOBleed is by looking at the iLO user interface — the interface is different on a compromised device. On the other hand, the company noted that the attackers might take steps in the future to prevent this detection method.
Amnpardaz is working on a tool that can be used to verify the integrity of the firmware.
Related: FiveSys Rootkit Abuses Microsoft-Issued Digital Signature
Related: Shrootless: macOS Vulnerability Found by Microsoft Allows Rootkit Installation
Related: Diplomatic Entities Targeted with New ‘Moriya’ Windows Rootkit
















