
A critical crypto-related vulnerability that can be exploited to manipulate votes without being detected has been found to impact e-voting systems in Switzerland and Australia.
The Swiss government, specifically the Swiss Post national postal service, announced last month the launch of a public bug bounty program for its electronic voting systems, with rewards of up to $50,000.
Switzerland has been conducting e-voting trials since 2004 and Swiss Post believes it has now developed a fully verifiable system that can make e-voting widely available in the country. While the organization has contracted a third-party to test the security of the new e-voting system, it has also decided to launch a public bug bounty program. The project will run until March 24 and over 3,000 hackers from around the world have signed up.
A team of researchers calling itself setuid(0) has identified a significant number of vulnerabilities in the code, but Swiss Post has mostly classified them as “low risk.”
Shortly after Swiss Post announced the bug bounty program, cryptography experts Sarah Jamie Lewis and Matthew Green pointed out that there were some potentially serious issues in the cryptographic functions.
On Tuesday, Lewis, along with researchers Olivier Pereira and Vanessa Teague, disclosed the details of a serious crypto-related issue that they claim can be exploited for “undetectable vote manipulation.” The same vulnerability was also independently discovered by two other researchers.
The vulnerability is present in functionality whose role is to ensure that anyone can verify the correctness of an election. The concept of “universal verifiability” guarantees that votes have not been tampered with even if all server-side components have been compromised. The Swiss voting system relies on “complete verifiability,” which offers the same guarantees as long as at least one server-side component has not been compromised. However, researchers found that this e-voting system fails to ensure complete verifiability.
“In the SwissPost system, encrypted electronic votes need to be shuffled to protect individual vote privacy. Each server who shuffles votes is supposed to prove that the set of input votes it received corresponds exactly to the differently-encrypted votes it output. This is intended to provide an electronic equivalent of the publicly observable use of a ballot box or glass urn,” the researchers explained.
The problem, according to the experts, is that this shuffling process relies on a cryptographic primitive known as a trapdoor commitment scheme, which allows anyone who knows the trapdoor values to alter votes without leaving any trace.
Exploitation of this vulnerability is not an easy task as it requires deep access to the e-voting system and expert knowledge. Swiss Post, which highlighted that the flaw does not allow malicious actors to infiltrate voting systems, stated that the weakness can only be exploited by someone who has control over its IT infrastructure and even then they would need assistance from insiders.
However, Lewis, who is the executive director of a privacy-focused non-profit called Open Privacy, pointed out on Twitter that the goal of their research is not to show that someone from the outside can tamper with elections, but that Swiss Post itself can modify votes without leaving a trace.
“This isn’t ‘some random hacker can steal an election,’ this is ‘Swiss Post can prove they didn’t steal an election, even if they did’,” she explained.
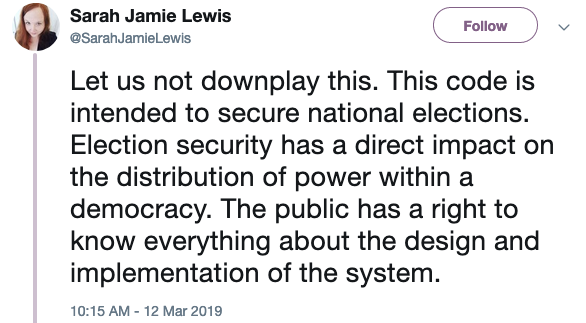
Lewis, Pereira and Teague have not reported their findings through the Swiss Post’s bug bounty program. Lewis claims they are aware of other issues in the code, but says they are not as critical. “This code is simply not up to the standard we should require of critical public infrastructure,” she said.
In its statement on the matter, Swiss Post claimed the vulnerability was actually first identified back in 2017, but it was not fully addressed by Scytl, the Spain-based electronic voting solutions provider that develops the system for the Swiss government.
Scytl has now made some changes that should fully address the problem, but the company has downplayed the findings, stating that “in practice, such attacks are highly unlikely — not to say impossible — to perform.”
The Federal Chancellery of Switzerland, the agency in charge of organizing federal elections, has also released a statement, pointing out that the vulnerability does not impact systems currently in use.
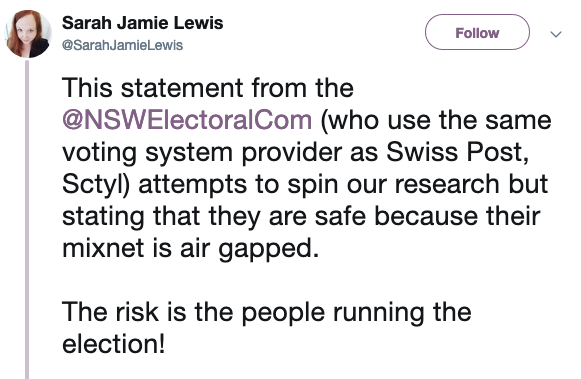
It has been revealed that the same voting system made by Scytl is also used in the Australian state of New South Wales. The NSW Electoral Commission has also downplayed the risk, arguing that the machine that would need to be targeted in an attack is air-gapped.
“In order for this weakness to be an issue, a person would need to gain access to the physical machine. They would need all the right credentials and the right code to alter the software,” a spokesperson for the NSW Electoral Commission stated. “Our processes reduce this risk as we specifically separate the duties of people on the team and control access to the machine to reduce the potential for an insider attack. Scytl is delivering a patch which will be tested and implemented shortly to address this matter.”
Related: Securing the Vote Against Increasing Threats
Related: Electronic Voting – The Greatest Threat to Democracy
Related: Georgia’s Use of Electronic Voting Machines Allowed for Midterms














