Security researchers from Bitdefender have warned that a new instant messaging Trojan has infected hundreds of computers all over the world.
Identified as Gen:Variant.Downloader.167 by Bitdefender, the malware distributes itself through Facebook’s instant messaging feature and Yahoo Messenger.
Experts say the Trojan relies on “polite” messages, which it sends from infected computers to users from the victim’s contact list. The malicious messages read something like this: “I want to post these pictures on Facebook, do you think it’s OK?”
The messages are accompanied by links to popular file sharing services like Fileswap and Dropbox where the threat is hosted. Bitdefender experts have told SecurityWeek that the malicious file is first executed without parameters. The malware then creates a folder with a random name in Application Data and it copies itself to this folder with a random name and an “.exe” extension.
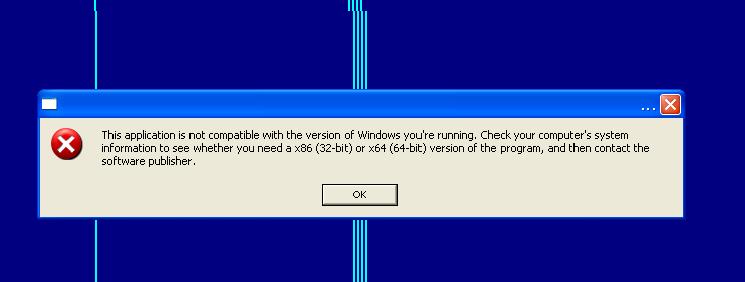
Then, it creates a registry entry in “HKCU\Software\Microsoft\Windows\CurrentVersion\Run” with the name Counter Background WWAN Thread Mapper User NetBIOS. Once all this is done, the victim is presented with the following error message in an effort to avoid raising any suspicion: “This application is not compatible with the version of Windows you’re running. Check your computer’s system information to see whether you need a x86 (32-bit) or x64 (64-bit) version of the program, and then contact the software publisher.”
Another executable file with a random name is created in the same folder in Application Data. This file is executed with two parameters: WATCHDOGPROC, and the path to the first executable file.
Finally, a configuration file is created in the same folder, and the malware connects to a command and control server.
According to Bitdefender, Cybercriminals can command the Trojan to download other pieces of malware and eventually harvest confidential data, such as usernames, passwords and even banking credentials.
“The Trojan hides some of its encrypted data between biblical verses. The data is eventually decrypted with numbers generated by a mathematical processor,” Bitdefender Security Specialist Bianca Stanescu told SecurityWeek.
The largest number of infections have been spotted in Romania, Germany and Canada. However, infected computers are also located in the United States, the United Kingdom, France and Denmark.
















