macOS High Sierra is plagued by a bug that can be exploited to gain root access to a machine by leaving the password field blank. Apple is expected to quickly release a patch, especially since remote exploitation is also possible.
Ever since High Sierra came out, some users have complained that their admin accounts had become standard accounts after updating the operating system. While trying to find a solution for the problem, one user on Apple’s Developer Forums suggested logging in with “root” and no password in order to obtain the access needed to create an admin account.
This solution was suggested on November 13, and on November 28 someone realized that logging in to the root account with no password should not be possible and that this is a major vulnerability.
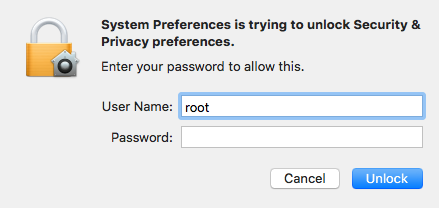
Gaining root access via this flaw requires entering the “root” username in the graphical user interface (GUI) and leaving the password field blank. A couple of attempts are required, but SecurityWeek can confirm that it’s easy to reproduce.
Access “System Preferences” from the Apple menu and click on any of the categories that require administrator privileges in order to make changes (e.g. Security & Privacy, Users & Groups, Parental Controls). Then click on the lock icon in the bottom left corner of the window and enter the username “root” with a blank password when prompted. Hit the Enter key or the Unlock button twice and root access is granted.
An analysis of the flaw revealed that an attempt to log in as root with a blank password actually activates a subroutine that creates the root account, which Apple has disabled by default. Once the root account has been activated, logging in as root with no password works on the first try.
While it may appear that the vulnerability can only be exploited by having physical access to the targeted machine, macOS hacker Patrick Wardle and others have managed to reproduce it remotely as well if sharing services are enabled on the device. Some experts warned that malicious actors could be scanning the Web for remotely accessible computers that they can attack using this security hole.
Apple is working on patching the vulnerability. In the meantime, users can protect themselves against potential attacks by manually setting a password for the root user. Disabling sharing services is also a good way to prevent remote exploitation of the flaw.
This is the second password-related bug found in macOS High Sierra recently. Back in October, a developer noticed that the operating system had leaked the passwords for encrypted Apple File System (APFS) volumes via the password hint.
UPDATE. Apple has already released an update for High Sierra to patch this vulnerability, which the company tracks as CVE-2017-13872.
An expert also pointed out that the vulnerability can be exploited with any password, not just a blank. The entered password will be the password that is set for the root account.
Related: Unsigned Apps Can Steal macOS Keychain Passwords
Related: Apple Silently Patched macOS Security Bypass Flaw
Related: macOS High Sierra Update Patches Keychain Access Flaw













