The Ohio Lottery cyberattack conducted last year by a ransomware group has impacted more than half a million individuals, the lottery said this week.
The incident came to light in late December 2023, after the Ohio Lottery announced shutting down some systems in an effort to contain the breach.
At around the same time, a seemingly new ransomware group named DragonForce took credit for the attack.
The hackers have since made available more than 90 Gb of files (in .bak backup format) allegedly stolen from the Ohio Lottery. They claim to have obtained more than 1.5 million records of employee and player information, including names, email and postal addresses, winnings, dates of birth, and social security numbers.
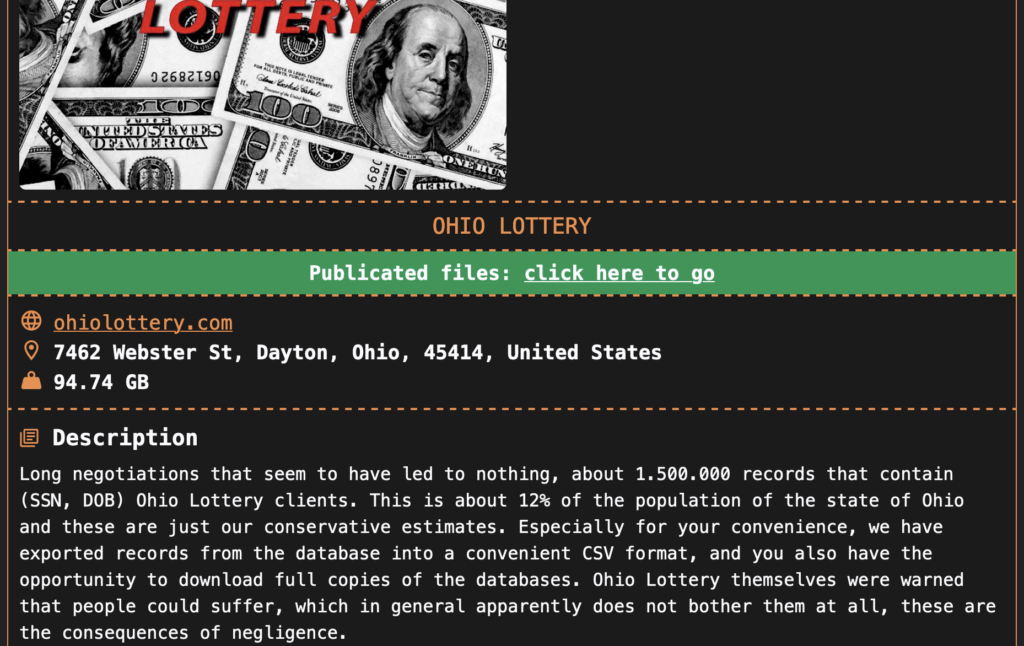
It’s worth noting that the ransomware group initially claimed to have stolen 3 million records.
The Ohio Lottery told the Maine Attorney General on Thursday that roughly 538,000 individuals are impacted. The report sent to the AG and the letter sent to impacted individuals confirms that full names and social security numbers have been compromised.
The organization says it has no evidence that the stolen information has been or will be misused, but it has decided to offer free credit monitoring and identity theft protection services to impacted individuals.
The DragonForce leak website currently names more than 40 victims from around the world.
Cyble reported recently that it had found a DragonForce ransomware binary based on LockBit Black ransomware, suggesting that DragonForce used a leaked LockBit Black builder to generate its binary.
Related: City of Wichita Shuts Down Network Following Ransomware Attack
Related: Brandywine Realty Trust Hit by Ransomware
Related: LockBit Takes Credit for City of Wichita Ransomware Attack

