Sustainable energy giant Hitachi Energy has blamed a data breach affecting employees on the exploitation of a recently disclosed zero-day vulnerability in Fortra’s GoAnywhere managed file transfer (MFT) software.
In a press release published on Friday, Hitachi Energy said the Cl0p ransomware gang targeted the GoAnywhere product and may have gained unauthorized access to employee data in some countries.
“Upon learning of this event, we took immediate action and initiated our own investigation, disconnected the third-party system, and engaged forensic IT experts to help us analyze the nature and scope of the attack,” Hitachi Energy said. “Employees who may be affected have been informed and we are providing support. We have also notified applicable data privacy, security and law enforcement authorities and we continue to cooperate with the relevant stakeholders.”
The company has found no evidence that its network operations and customer data have been compromised.
The statement was published after the Cl0p (aka Clop) cybercrime group named Hitachi Energy on its Tor-based leak website. By naming the company on their site, the hackers are threatening to leak stolen data unless a ransom is paid soon.
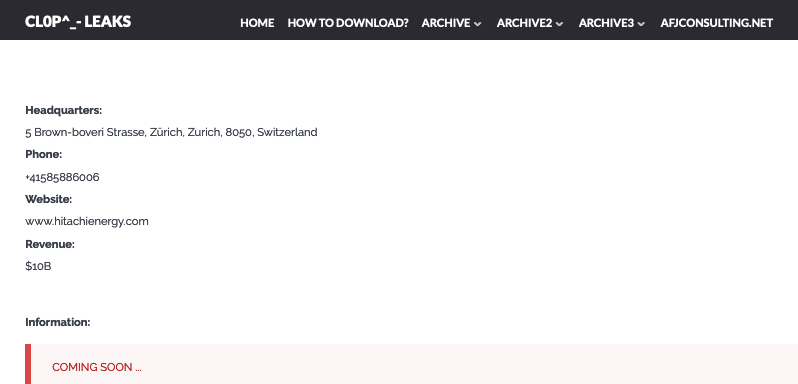
Hitachi Energy has its global headquarters in Switzerland. The company serves organizations in the utility, industrial, and infrastructure sectors across 140 countries, and employs roughly 40,000 people.
The vulnerability exploited in the attack is CVE-2023-0669, a remote code execution flaw whose existence was disclosed by Fortra on February 1, after attacks exploiting it were detected. A patch was released a week later.
Exploitation of CVE-2023-0669 has been linked to the Cl0p ransomware group, which claimed to have used the zero-day to breach more than 130 organizations. It appears that the hackers leveraged the security hole to gain access to data stored on servers associated with the Fortra product.
To date, only California-based digital bank Hatch Bank, healthcare provider Community Health Systems, and cybersecurity firm Rubrik have publicly admitted being hit.
The Cl0p gang has started leaking files allegedly stolen from Rubrik and Hatch Bank, which indicates that the two companies have refused to pay the ransom demanded by the cybercriminals.
Community Health Systems has not been named on the Cl0p leak site. In the case of the healthcare organization, as many as one million patients may be impacted.
Related: Microsoft SmartScreen Zero-Day Exploited to Deliver Magniber Ransomware
Related: Ransomware Group Claims Theft of Valuable SpaceX Data From Contractor
Related: CISA Program Warns Critical Infrastructure Organizations Vulnerable to Ransomware Attacks

