Cloud data management and data security firm Rubrik has confirmed being targeted in an attack exploiting a recent GoAnywhere zero-day vulnerability after a ransomware group named the company on its leak website.
Fortra, previously known as HelpSystems, alerted users of its GoAnywhere managed file transfer (MFT) software on February 1 about a zero-day remote code injection exploit. The company released a patch for the vulnerability, tracked as CVE-2023-0669, roughly one week later.
The attacks were quickly linked to a financially motivated threat group known for conducting attacks involving the Cl0p (Clop) ransomware. The hackers exploited the vulnerability to gain access to the information of GoAnywhere customers, which they plan on using to extort victims.
Soon after the attacks came to light, the ransomware gang’s representatives told Bleeping Computer that more than 130 organizations were hit through the GoAnywhere zero-day exploit.
However, only a handful of victims have come forward to date. The list includes California-based digital bank Hatch Bank and healthcare provider Community Health Systems.
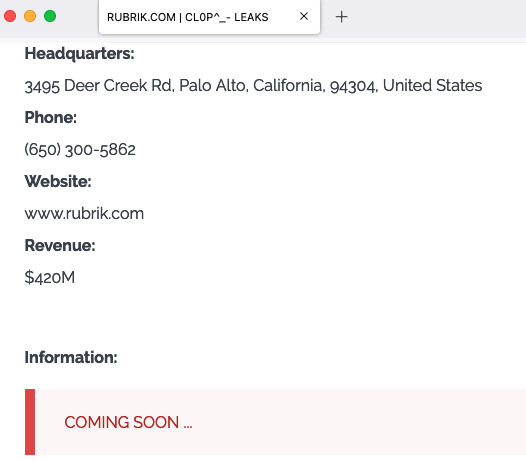
California-based Rubrik has now also confirmed getting hacked after being named by the Cl0p ransomware group on its Tor-based leak website.
Michael Mestrovich, Rubrik’s CISO, said in a statement on Tuesday that the company detected unauthorized access to a “limited amount of information” in one of its non-production IT testing environments.
Rubrik’s investigation, conducted with assistance from outside experts, has not found evidence that data secured on behalf of customers has been compromised. There is also no evidence of lateral movement to other systems.
“Rubrik has been conducting a thorough, comprehensive review of the involved data in partnership with a third-party firm,” Mestrovich said. “The involved data mainly consists of Rubrik internal sales information, which includes certain customer and partner company names, business contact information, and a limited number of purchase orders from Rubrik distributors. The third-party firm has also confirmed that no sensitive personal data such as social security numbers, financial account numbers, or payment card numbers were exposed.”
In the case of Hatch Bank, the information of roughly 140,000 customers was compromised and the bank is facing class action lawsuits over the incident.
Community Health Systems, which is one of the largest healthcare providers in the US, estimated that as many as one million patients may have been impacted.
In addition to Rubrik, the Cl0p group has added Hatch Bank to its leak website. It’s unclear if any other organizations currently listed on their site have been breached through the GoAnywhere attack.
For Hatch Bank and Rubrik, the cybercriminals published several screenshots showing the type of data they have obtained. They have suggested that more data will be leaked unless their demands are met.
Related: Microsoft SmartScreen Zero-Day Exploited to Deliver Magniber Ransomware
Related: Ransomware Group Claims Theft of Valuable SpaceX Data From Contractor
Related: CISA Program Warns Critical Infrastructure Organizations Vulnerable to Ransomware Attacks

