While the number of services affected by the OpenSSL flaw known as Heartbleed has decreased, the Shodan search engine has still found nearly 200,000 vulnerable devices.
Heartbleed, tracked as CVE-2014-0160, is a critical vulnerability that allows attackers to steal information protected by SSL/TLS encryption. Some researchers believe the flaw was used in an attack where hackers managed to steal 4.5 million healthcare records.
A search for vulnerable devices conducted by Shodan in November 2015 returned 238,000 results and the number dropped by roughly 1,000 by late March 2016. A new search carried out on Sunday showed that 199,594 services are still vulnerable to Heartbleed attacks.
Many of the affected devices are located in the United States (42,000), followed by South Korea (15,000), China (14,000), Germany (14,000), France, (8,700), Russia (6,600), UK (6,500), India (5,800), Brazil (5,500) and Italy (4,800). HTTPS accounts for a large majority of impacted services.
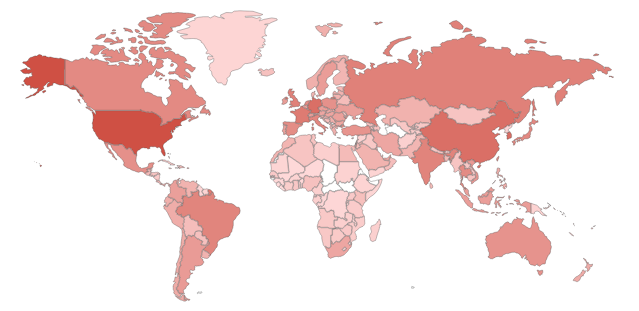
South Korea occupied only the 8th place after previous scans, but it has now become the second most affected country, apparently due to devices operated by SK Broadband, Boranet and KT Corporation (formerly Korea Telecom).
The list of top affected organizations also includes Amazon, Verizon Wireless, German ISP Strato, OVH in France, German hosting firm 1&1 Internet, Comcast, and Taiwan-based HiNet.
Apache HTTP Server (httpd) is by far the most affected product, particularly versions 2.2.22 and 2.2.15, while the top operating system is Linux 3.x. Shodan also found that more than 70,000 of the affected services have expired SSL certificates.
Related Reading: Organizations Slow at Patching Heartbleed in VMware Deployments
Related Reading: Many Cisco Devices Still Vulnerable to NSA-Linked Exploit
Related Reading: DROWN Vulnerability Still Unpatched by Most Cloud Services













