Several malware families are being delivered using the recently disclosed Windows vulnerability identified as Follina and CVE-2022-30190, which remains without an official patch.
The vulnerability, related to the Microsoft Support Diagnostic Tool (MSDT), can be exploited for remote code execution using specially crafted documents. While the root cause of the security hole appears to have been known for at least a couple of years, Microsoft appears to have largely ignored the issue until now.
The existence of the flaw came to light after a researcher spotted a document exploiting it. There is indication that attacks started in April, with users in India and Russia being targeted.
Proofpoint reported this week that a major cybercrime group tracked as TA570 has exploited CVE-2022-30190 to deliver Qbot, a widely used information stealer that is also known as Qakbot and Pinkslipbot. The malware can spread on the compromised network and it has been leveraged for initial access by several cybercrime groups.
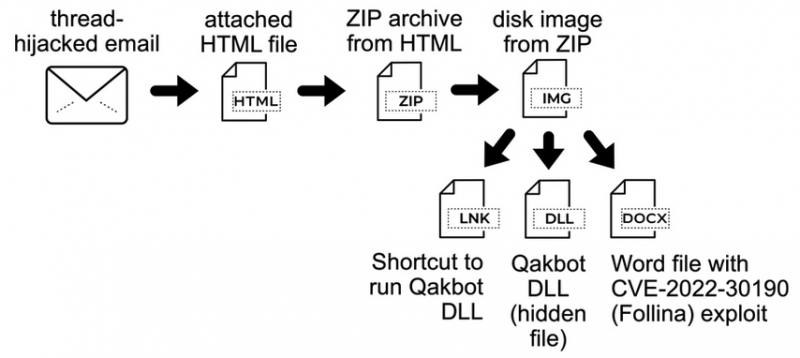
The attackers delivered the exploit by attaching specially crafted HTML files to hijacked email conversations. The SANS Institute has published a technical analysis of these attacks, along with indicators of compromise (IoCs).
Proofpoint previously reported that a threat actor linked to China, TA413, had been exploiting Follina in attacks aimed at the Tibetan community.
Broadcom’s Symantec division reported this week that malicious hackers have also exploited the flaw to deliver the AsyncRAT remote access trojan (RAT), which gives attackers control over the targeted system.
Both Qbot and AsyncRAT have been used by many threat groups.
Symantec has also observed attacks in which CVE-2022-30190 was exploited to deliver an unnamed information stealer.
Microsoft has yet to release an official fix, but workarounds, mitigations and third-party patches are available. Office Pro Plus, Office 2013, Office 2016, Office 2019 and Office 2021 have been confirmed to be affected.
Related: Cybersecurity Community Warned of Fake PoC Exploits Delivering Malware
Related: CISA Says ‘HiveNightmare’ Windows Vulnerability Exploited in Attacks













