Researchers have spotted fake proof-of-concept (PoC) exploits that appear to have been created by threat actors in an effort to deliver malware to members of the cybersecurity community.
On May 19, researchers reported that GitHub was hosting malicious software disguised as PoC exploits for a couple of Windows vulnerabilities that Microsoft fixed with its April 2022 Patch Tuesday updates.
The fake PoC exploits, which have since been removed by GitHub, were delivered as executable files that, when run, could open a backdoor to the system.
The PoCs claimed to target CVE-2022-24500 and CVE-2022-26809, both of which can be exploited for remote code execution on Windows systems. While there is no indication that the flaws have been leveraged in attacks, some cybersecurity companies did warn that they could pose a serious risk — CVE-2022-26809, for instance, is believed to be wormable.
Threat intelligence company Cyble has analyzed the fake PoC exploits and determined that threat actors were likely using them to target members of the infosec community. The company also found posts on cybercrime forums discussing the exploits.
The fake PoCs, which appeared to have been created by the same threat actor, were .NET binaries packed with an open source application protector named ConfuserEx. When executed, they displayed fake messages apparently showing a failed attempt to exploit CVE-2022-24500 or CVE-2022-26809.
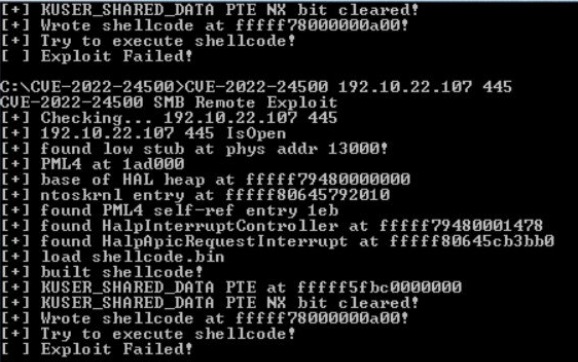
After executing this routine, the files ran a hidden PowerShell command that delivered the Cobalt Strike Beacon payload, which can be used to download additional malware and for lateral movement.
“Usually, people working in information security or TAs use exploits to check for vulnerabilities. Hence, this malware might only target people from this community. Therefore, it becomes essential for the Infosec Community members to check the credibility of sources before downloading any proof of concept,” Cyble explained.
It’s unclear if anyone actually executed the fake PoC exploits and if their systems did get compromised. However, some members of the community pointed out that researchers would likely test the fake exploits in a sandboxed environment, which would significantly limit impact.
It’s not uncommon for threat actors to target the cybersecurity community. Last year, Google warned that North Korean hackers had been targeting security researchers at various companies and organizations, using zero-day vulnerabilities, fake social media profiles, malicious websites, and they had even set up a fake penetration testing company.
Related: PoC Exploit Published for Latest Microsoft Exchange Zero-Day
Related: PoC Exploit Released for Wormable Windows Vulnerability
Related: Google Releases PoC Exploit for Browser-Based Spectre Attack













