Malicious actors are increasingly abusing free cloud services, which has led to a significant spike in botnet scanning activity, according to performance and security solutions provider Netscout.
Netscout typically sees 10,000-20,000 IP addresses conducting internet scans every day. However, the company observed an increase to more than 35,000 devices on December 8 and another spike that reached 43,000 devices on December 20.
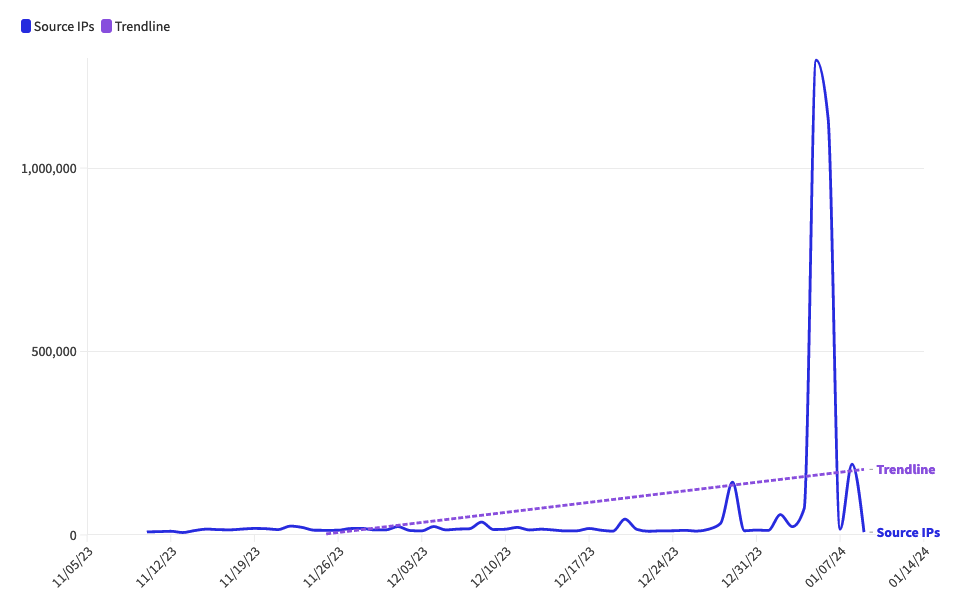
The number of source IPs associated with scanning activity saw a sharp increase on several days since, peaking on January 5, with nearly 1.3 million IPs. A majority of the IPs are associated with the US, China, Vietnam, Taiwan and Russia, Netscout reported.
“Analysis of the activity has uncovered a rise in the use of cheap or free cloud and hosting servers that attackers are using to create botnet launch pads. These servers are used via trials, free accounts, or low-cost accounts, which provide anonymity and minimal overhead to maintain,” the company explained in a blog post.
Netscout believes the scanning represents reconnaissance activity, with hackers using these new botnets to find vulnerabilities they can exploit.
The most commonly targeted ports are associated with HTTP, HTTPS, RDP, SIP, and other types of web servers, and there has also been an increase in scanning for email servers.
“The unprecedented growth of malicious botnets in the cloud confirms that a dangerous new wave of cybercrime is underway. This battle is just beginning and the adversary is performing reconnaissance to uncover areas to exploit,” Netscout said.
Related: Mysterious Malware Uses Wi-Fi Scanning to Get Location of Infected Device
Related: Mozi Botnet Likely Killed by Its Creators
Related: Multiple DDoS Botnets Exploiting Recent Zyxel Vulnerability
















