The recent shutdown of the Mozi botnet is believed to be the work of its operators, who may have been forced to kill their creation by Chinese authorities.
This is a theory from cybersecurity firm ESET, whose researchers recently discovered a kill switch suggesting that the takedown was deliberate.
Mozi emerged in September 2019 and at one point it was a highly active botnet, accounting for a large chunk of the traffic associated with IoT botnets. In June 2021, a unit of the Chinese cybersecurity firm Qihoo 360 reported seeing 1.5 million infected nodes, including more than 800,000 in China and many in India.
Weeks later, the cybersecurity company announced helping law enforcement arrest the alleged developers of Mozi, but noted that its peer-to-peer (P2P) architecture would likely keep the botnet alive, enabling it to continue spreading.
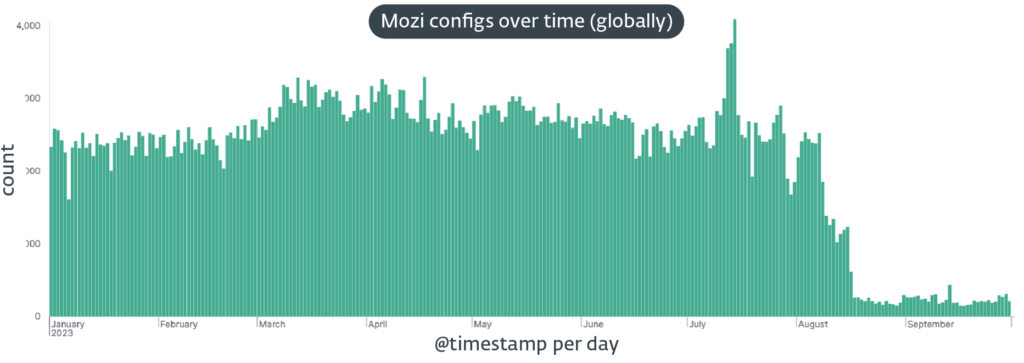
Before the significant drop in Mozi activity observed in August, ESET had been seeing thousands of infections every day. The number of daily infections observed by the company became insignificant in August, with the first drop seen in India, on August 8, and the second in China, on August 16.
In late September, ESET identified a kill switch that had been used to take down the botnet. The kill switch involved a control payload instructing bots to download and install an update over HTTP.
The update ensures that while the malware remains on systems, it no longer performs its malicious routines. Actions initiated by the kill switch include killing the parent process associated with the Mozi malware, disabling some system services, executing router and other device configuration commands, and disabling access to certain ports.
“Our analysis of the kill switch shows a strong connection between the botnet’s original source code and recently used binaries, and also the use of the correct private keys to sign the control payload,” ESET noted.
The company’s theory is that the takedown of the Mozi botnet was deliberately initiated by its creators, with Chinese law enforcement possibly forcing them to cooperate.
“The demise of one of the most prolific IoT botnets is a fascinating case of cyberforensics, providing us with intriguing technical information on how such botnets in the wild are created, operated, and dismantled,” ESET said.
Related: Qakbot Hackers Continue to Push Malware After Takedown Attempt
Related: US Announces Takedown of Card-Checking Service, Charges Against Russian Operator
Related: Takedown of GitHub Repositories Disrupts RedLine Malware Operations

