The hackers behind a cyberespionage campaign known as Blackgear are back with improved malware that abuses social media websites, including Facebook, for command and control (C&C) communications.
The threat group, also known as Topgear and Comnie, has been around since at least 2008, mainly targeting entities in Taiwan, South Korea and Japan. Their objectives include organizations in the telecommunications, defense, government, aerospace, and high-tech sectors. Some limited evidence suggests that the attacks may be conducted by Chinese state-sponsored actors.
Previous Blackgear attacks involved malware tracked as Elirks and Protux, which the hackers created themselves. The latest attacks, analyzed by Trend Micro, relied on a new version of the Protux backdoor and a downloader named Marade.
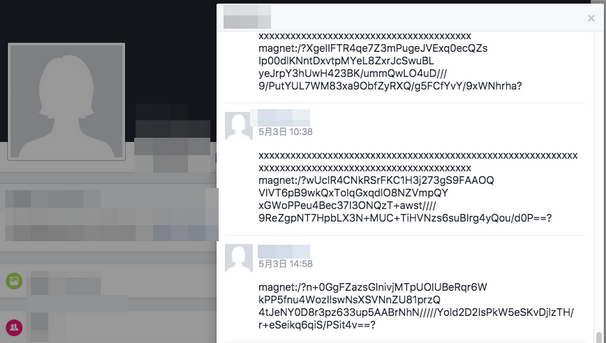
One interesting technique leveraged by the threat group involves using blogs and social media websites for C&C communications, which helps it easily change C&C servers and improve its chances of evading detection. In the past, the actor posted encrypted C&C configurations on websites such as github.com, tumblr.com and blogspot.com. The more recent attacks also abuse Facebook to store and retrieve C&C data.
The more recent attacks start with an email delivering a fake installer or decoy document, which drop the Marade downloader. The downloader is placed in a file whose size exceeds 50 Mb in an effort to bypass traditional sandbox products.
Marade checks the infected system for an antivirus solution and retrieves C&C data from a blog or social media post. If the compromised machine is of interest, the Protux backdoor is downloaded.
Protux allows the attackers to list all the files, processes, services and registries on the compromised host, along with taking screenshots and creating a shell that provides access to the system.
“Blackgear has been targeting various industries since its emergence a decade ago. Its apparent staying power stems from the furtive ways with which its attacks can evade traditional security solutions,” Trend Micro researchers explained. “For instance, Blackgear employs two stages of infection for each of its attacks. The potential victim may not be able to notice the intrusions as the first stage involves only profiling and reconnaissance. And once infection with a backdoor occurs, typical red flags may not be raised as it abuses microblogging and social media services to retrieve information needed for C&C communication.”
Researchers have also stumbled upon a tool that provides the user interface from which the hackers control the Protux and Marade malware.
“Based on the controller’s behavior, we can posit that both Marade and Protux were authored by the same threat actors,” experts noted.
Related: China-Linked APT15 Develops New ‘MirageFox’ Malware
Related: Chinese Cyberspies Target National Data Center in Asia

