Apple has pulled its latest Rapid Security Response updates for iOS and macOS after users complained that they were getting errors when accessing some websites through Safari.
The company informed users on Monday that it had released macOS Ventura 13.4.1 (a), iOS 16.5.1 (a), and iPadOS 16.5.1 (a). These Rapid Security Response updates, as well as Safari 16.5.2, address an actively exploited WebKit vulnerability tracked as CVE-2023-37450.
Reported by an anonymous researcher, the zero-day flaw can be exploited for arbitrary code execution by getting the targeted user to access malicious web content.
The goal of Rapid Security Response updates is to quickly deliver zero-day vulnerability fixes to iPhones and Macs, ensuring that users get critical patches without having to wait for regular operating system updates.
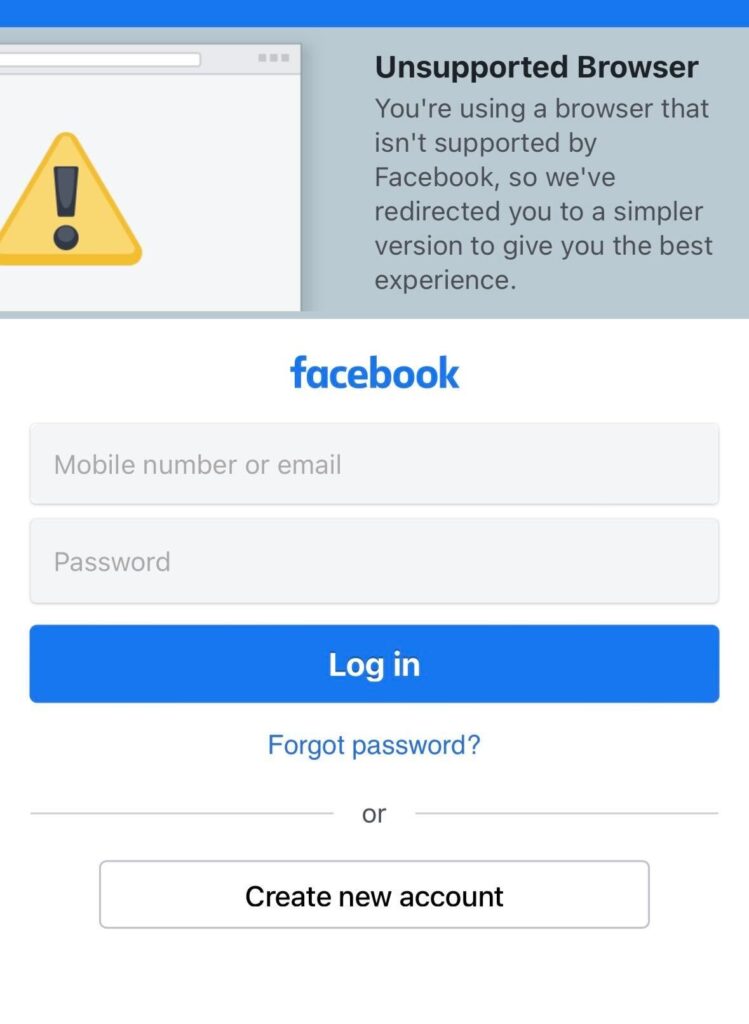
However, shortly after Apple announced the patches for CVE-2023-37450, users started complaining that they were getting errors when trying to access Facebook, Instagram, Zoom and other websites after installing the update.
The tech giant quickly confirmed the issue and pulled the iOS and macOS updates.
“Apple is aware of an issue where this Rapid Security Response might prevent some websites from displaying properly,” the company said on Tuesday. “Rapid Security Responses iOS 16.5.1 (b), iPadOS 16.5.1 (b), and macOS 13.4.1 (b) will be available soon to address this issue.”
Users who are experiencing issues can remove the buggy update by following the instructions provided by Apple.
Rapid Security Response patches can be a good way to protect users against zero-day exploits, but the fact that their development is rushed means they might not be as rigorously tested as regular patches.
While it’s not uncommon for tech giants to push out buggy updates, if Apple’s Rapid Security Responses continue causing problems, many users could refuse to install them until they are properly tested, which would defeat the purpose of rapid patches.
iPhone users also had problems installing Apple’s first Rapid Security Response update, which the company released in May.
Related: Apple Patches 3 Exploited WebKit Zero-Day Vulnerabilities
Related: Apple Patches iOS Flaws Used in Kaspersky ‘Operation Triangulation’
Related: Apple Patches Actively Exploited WebKit Zero-Day Vulnerability


