Exploit acquisition firm Zerodium on Monday announced that it’s offering significantly higher payouts for many types of exploits, including up to $2 million for remote iOS jailbreaks and $1 million for vulnerabilities in popular chat applications.
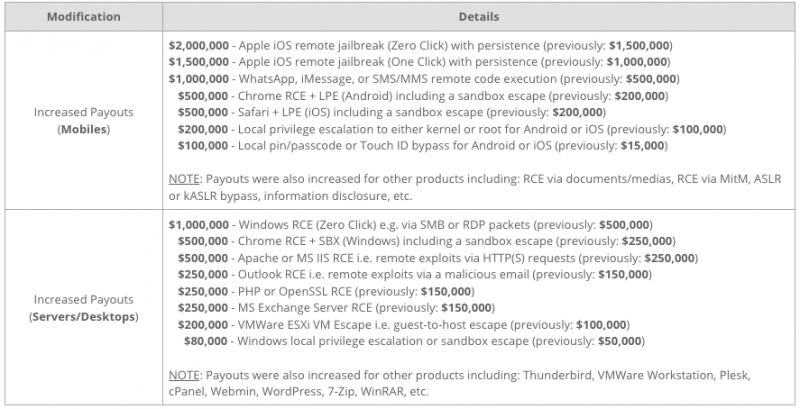
Zerodium is now prepared to pay up to $2 million for persistent iOS jailbreaks that can be executed remotely without any user interaction – the amount has been increased from $1.5 million. Hackers can now earn $1.5 million for a remote iOS jailbreak that requires minimal user interaction (i.e. one click).
Payouts for remote code execution vulnerabilities affecting WhatsApp, iMessage or SMS/MMS applications have now doubled to $1 million.
Researchers can earn half a million dollars if they sell their Chrome (on Android) and Safari (on iOS) exploits to Zerodium, but their exploits must include remote code execution, privilege escalation and a sandbox escape.
It’s also worth noting that local PIN or TouchID bypass techniques for Android and iOS devices are now worth up to $100,000, a significant increase from the $15,000 offered by Zerodium until now.
In the desktop and servers category, the zero-day exploit broker has doubled the maximum payout – from $500,000 to $1 million – for a Windows exploit chain that achieves remote code execution via SMB or RDP packets without any user interaction.
Rewards have also doubled, to $500,000, for Chrome, Apache and Microsoft IIS exploits. Zerodium has also added $100,000 to rewards for remote code execution flaws in Outlook, Microsoft Exchange Server, PHP and OpenSSL.
Zerodium recently disclosed a NoScript zero-day that could have been exploited to execute arbitrary JavaScript code in the Tor Browser even if the maximum security level was used. Chaouki Bekrar, the company’s CEO, told SecurityWeek at the time that they had acquired high-end Tor exploits, which Zerodium customers had used to “fight crime and child abuse, and make the world a better and safer place for all.”
Zerodium says its zero-day exploits can only be acquired by a very limited number of governments and corporations, but these types of services have been highly controversial due to the potential for abuse.
Related: Zerodium Offers $1 Million for Tor Browser Exploits












