Rumors of the password’s demise have been greatly exaggerated over the years. As security professionals, we know how fragile they are in the hands of talented hackers, and how much users revile them, yet their ubiquity has proven stubborn to dislodge.
Last week, Yahoo introduced “Account Key”, which uses push notifications to their Yahoo Mail app on mobile devices. You can read more about the new approach, but in a nutshell; the notifications present the user with simple yes or no buttons to allow or deny login to Yahoo Mail on any other device (such as your desktop). You still have to type in your account name on yahoo.com, but Yahoo Mail immediately recognizes the account as enabled for Account Key and launches the notification via the app on that users’ pre-registered mobile device.
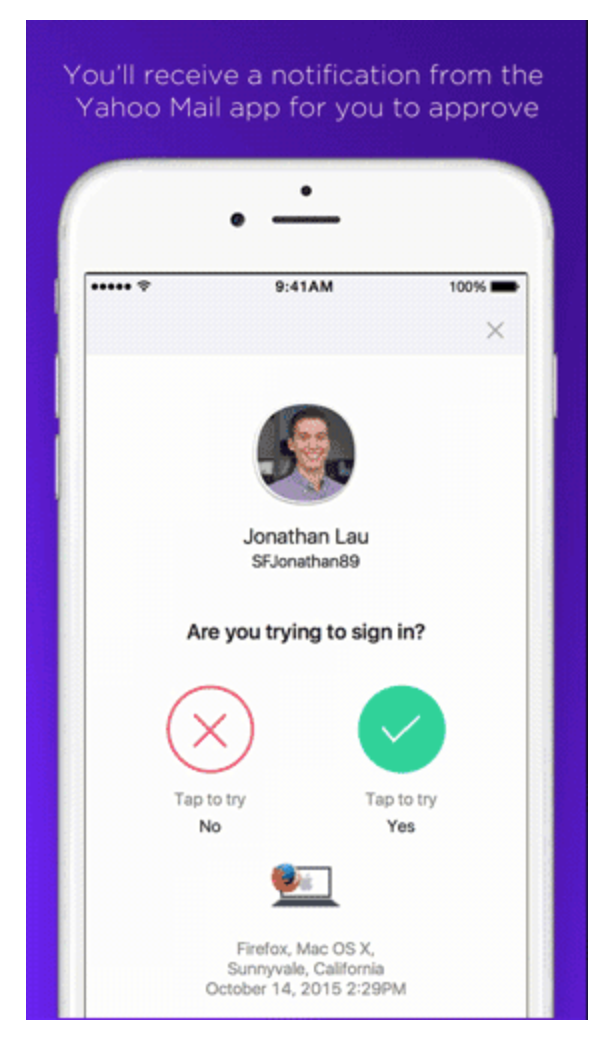 What’s different in this approach is that it takes full advantage of the availability and power of mobile devices. Availability, in the sense that a significantly large percentage of Yahoo Mail users possess a mobile device, at least partially addressing the ubiquity need that has kept passwords entrenched. Power, in the sense that it simplifies the user interaction to a new minimum, taking care of the authentication handshakes in the background.
What’s different in this approach is that it takes full advantage of the availability and power of mobile devices. Availability, in the sense that a significantly large percentage of Yahoo Mail users possess a mobile device, at least partially addressing the ubiquity need that has kept passwords entrenched. Power, in the sense that it simplifies the user interaction to a new minimum, taking care of the authentication handshakes in the background.
What about one-time passwords?
Yes, we already have one-time password apps or SMS that provide codes on mobile devices. But those require the user to enter that code on another device, making it less user-friendly than entering a password in the first place. Rather than make the user manually transfer a code from one device to the other to prove that they are in possession of the device, this approach takes care of that for them.
Is it really more secure?
Yahoo claims that it is, stating that “passwords are usually simple to hack”, but once you have Account Key, “even if someone gets access to your account info – they can’t sign in.” What is unknown is how the interaction between the app and Yahoo’s servers is managed. Is the user approval encrypted, for example? How susceptible would this be to a man in the middle attack?
Regardless, Yahoo has a point. Passwords are more susceptible to undetected theft than physical devices. But we can’t know for certain how much more secure this approach is until we know the architecture details.
Does this replace two-factor authentication?
The simple answer is no. Account Key relies only on something you have. Where the confusion may lie is that typical use of mobile device authentication is in addition to a password, which would be a combination of something you have and something you know. Because this method relies only on a single factor, it would not satisfy requirements for two-factor authentication by itself.
It should be made clear that this first iteration is for accessing Yahoo Mail only. Yahoo states that they will be rolling out Account Key to other Yahoo apps later this year. But if Account Key only ever supports the Yahoo ecosystem, then an opportunity will be missed.
The real value would be to extend Account Key as a service to provide access to apps provided by third parties. Perhaps there are efforts to make that happen already in progress. But Yahoo has shown the way – a technology that is both user friendly and secure has a great chance of finally eradicating the password and becoming the authentication technology of the future.











