Government agencies in the United States have made progress in the implementation of the DMARC standard in response to a Department of Homeland Security (DHS) directive, but the first deadline is less than two weeks away.
The Binding Operational Directive (BOD) 18-01 issued by the DHS in mid-October instructs all federal agencies to start using web and email security technologies such as HTTPS, STARTTLS and DMARC.
DMARC (Domain-based Message Authentication, Reporting and Conformance) is an email authentication, policy, and reporting protocol designed to detect and prevent email spoofing. Organizations can set the DMARC policy to “none” in order to only monitor unauthenticated emails, “quarantine” to send them to the spam or junk folder, or “reject” to completely block their delivery.
The DHS has ordered government agencies to implement DMARC with at least a “none” policy by January 15. Organizations will then need to set their DMARC policy to “reject” within one year.
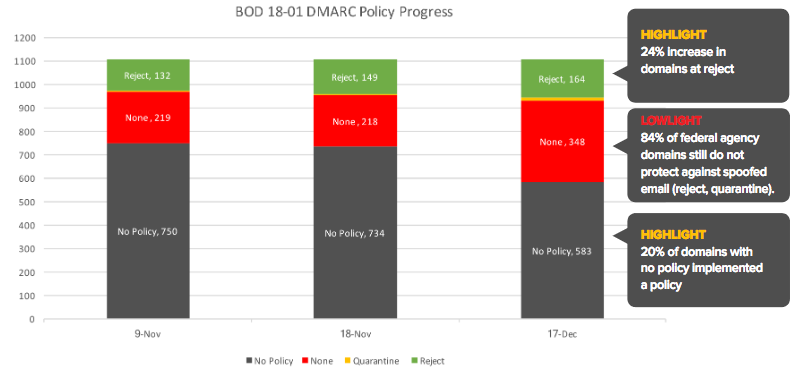
A few days after the DHS made the announcement, security firm Agari checked over 1,000 domains owned by federal agencies and found that only 18% had implemented DMARC. By mid-November it increased to 34% and in December it reached 47%.
However, only 16% of them had deployed “quarantine” or “reject” policies by December, an increase of two percentage points compared to the previous month.
More than 20 agencies have fully implemented DMARC, including the Federal Communications Commission (FCC), the Federal Trade Commission (FTC), the Senate, the Postal Service, the Department of Health and Human Services (HHS), and Department of Veterans Affairs.
The HHS has deployed DMARC across more than 100 of its domains, including ones used by Healthcare.gov, the National Institutes of Health (NIH), and the Centers for Disease Control and Prevention (CDC).
Agari said the overall email attack rate for government customers that had implemented DMARC dropped to less than one percent.
“Deploying a DMARC policy where p=none is simple, but it is only the first step,” Agari said in a report published on Tuesday. “To fully protect against phishing threats against both the federal government and the public at large (and maintain strong email governance), federal agencies must ultimately move to Quarantine and Reject policies.”
Related: DMARC Adoption Low in Fortune 500, FTSE 100 Companies
Related: DMARC in Higher Education – A Formidable Defense Against Targeted Scams
Related: Email Attacks Use Fake VAT Returns to Deliver Malware














