Many Fortune 500, FTSE 100 and ASX 100 companies have failed to properly implement the DMARC standard, exposing their customers and partners to phishing and other email-based attacks, according to email security firm Agari.
In a report titled “Global DMARC Adoption Report: Open Season for Phishers,” Agari, which in the past years has obtained tens of millions of dollars in funding, shared the results of its analysis into the adoption of DMARC.
DMARC (Domain-based Message Authentication, Reporting and Conformance) is an email authentication, policy, and reporting protocol designed to detect and prevent email spoofing.
Organizations using DMARC can specify what happens to unauthenticated messages: they can be monitored but still delivered to the recipient’s inbox (none), they can be moved to the spam or junk folder (quarantine), or their delivery can be blocked completely (reject).
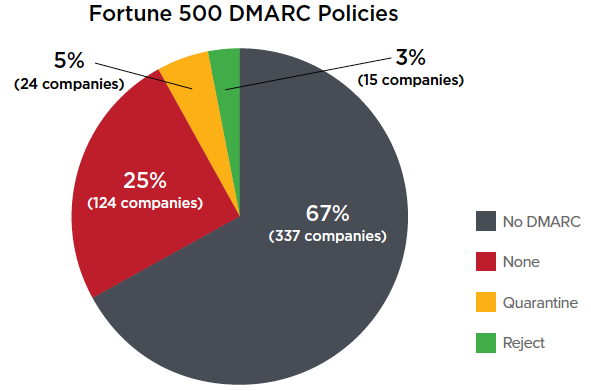
Agari’s analysis of public DNS records showed that only five percent of Fortune 500 companies have implemented a reject policy and three percent use the quarantine policy. Roughly two-thirds of these organizations have not published any type of DMARC policy.
The sectors with the highest adoption of the reject and quarantine policies are business services, financial, technology and transportation. The security firm has identified several sectors where not one organization has adopted these policies, including wholesales, motor vehicles, apparel, hospitality, food and drug stores, energy, aerospace, household products, chemicals, and engineering and construction.
In the case of Financial Times Stock Exchange (FTSE) 100 companies, the percentage is similar. Two-thirds have not implemented DMARC and only seven percent are using a reject or quarantine policy. Only a handful of real estate and financial services firms in the FTSE 100 have implemented proper DMARC policies.
An analysis of Australian Securities Exchange (ASX) 100 organizations showed that a DMARC policy is absent in 73 percent of cases. Only three companies from the utilities, industrial and consumer discretionary sectors have implemented a reject policy and one company in the materials sector is using a quarantine policy.
These figures are worrying considering that there are tens of thousands of phishing websites and their number has increased considerably in the past years.
Related: Top Websites Fail to Prevent Email Spoofing

