Security researchers at IBM have discovered a potentially serious vulnerability in a communications module made by Thales for IoT devices. Millions of devices could be impacted, but the vendor released a patch six months ago.
The flaw, tracked as CVE-2020-15858, was discovered in September 2019 and it was patched in February 2020. It was initially identified in Thales’ Cinterion EHS8 M2M module, which enables secure 3G and 4G communications in IoT devices, but it was later also found to impact ten other modules in the same product line.
The impacted modules are present in millions of IoT products, including ones used in the medical, telecom, energy and automotive industries.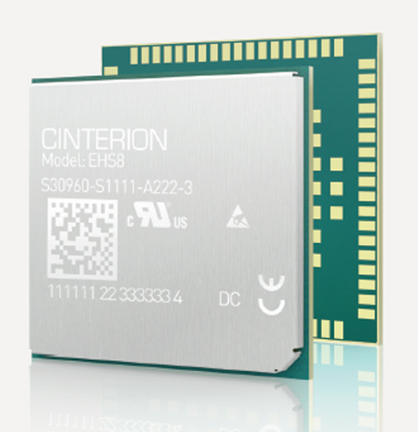
The vulnerability is related to the fact that the product runs Java code that can include information such as encryption keys, passwords and certificates. An attacker who has access to the targeted IoT device can exploit the vulnerability to bypass security mechanisms and gain access to this information, which can then be used to take control of a device or access the network housing it. In some cases, remote exploitation is possible via the communication capabilities provided by the module itself, IBM said.
The impact of an attack depends on what the targeted IoT device is used for. An attacker could, for example, target medical devices and manipulate readings or even tamper with the treatment delivered by the device (e.g. insulin pumps).
Another theoretical attack scenario described by IBM targets the energy and utilities sector. An attacker could hack smart meters and manipulate readings, which can lead to smaller or larger electricity bills.
“With access to a large group of these devices through a control network, a malicious actor could also shut down meters for an entire city, causing wide-reaching blackouts that require individual repair visits, or, even worse, damage to the grid itself,” IBM said in a blog post.
While a patch has been available for months, the company pointed out that it may not be an easy task to roll it out to some products, such as medical devices or industrial control systems (ICS). The patch can be delivered either via an update conducted over a USB connection or over the air, depending on the device’s capabilities.
Related: Black Hat Wrap-Up: IoT and Hardware Vulnerabilities Take the Spotlight
Related: Ripple20: Flaws in Treck TCP/IP Stack Expose Millions of IoT Devices to Attacks
Related: New Mirai Variant Targets Vulnerability in Comtrend Routers














