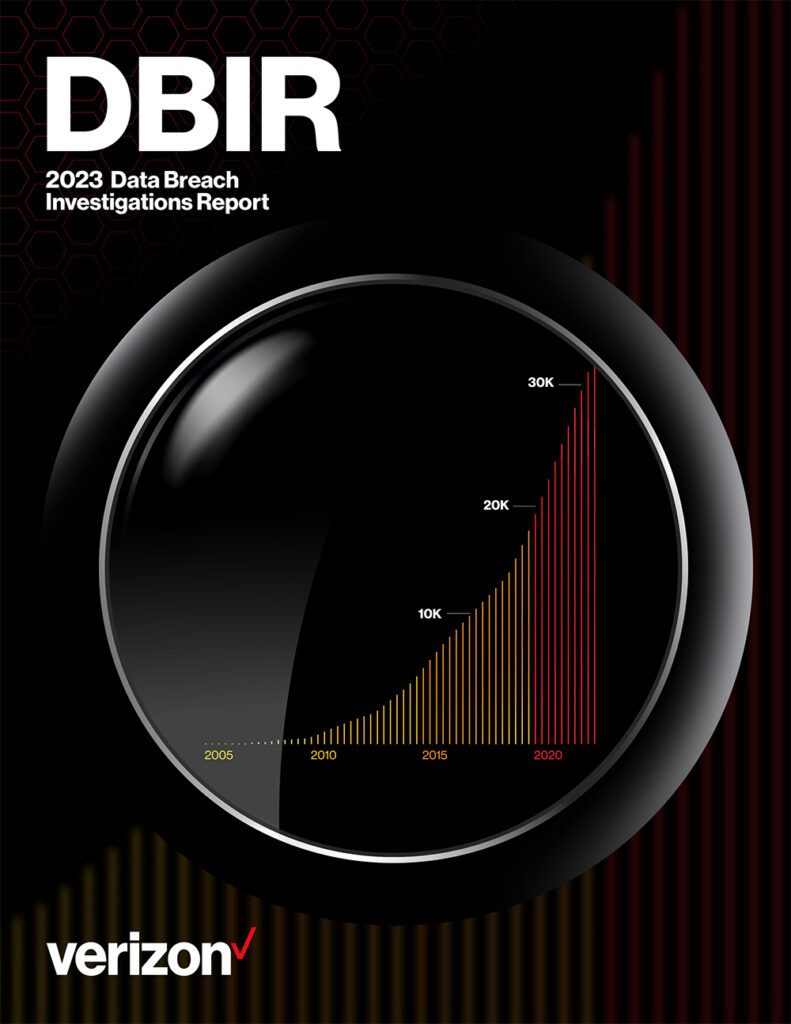
Verizon on Tuesday published its 16th annual Data Breach Investigations Report (DBIR) to provide organizations with useful information collected from incidents investigated by its Threat Research Advisory Center.
The DBIR is one of the cybersecurity industry’s most anticipated reports due to the fact that it’s based on the analysis of a significant number of real-world incidents. For the 2023 DBIR, Verizon analyzed more than 16,000 security incidents and roughly 5,200 breaches.
The report shows — based on data from the FBI — that the median cost of ransomware incidents has more than doubled over the past two years, to $26,000. Losses were only reported in 7% of cases, with victims losing between $1 and $2.25 million.
According to Verizon, the data shows “that the overall costs of recovering from a ransomware incident are increasing even as the ransom amounts are lower. This fact could be suggesting that the overall company size of ransomware victims is trending down. Even though the amounts requested by the threat actors would be smaller for those smaller companies—they want to get any money they can—the added costs of recovering their IT infrastructure under a backdrop of likely technical debt would spike their overall losses.”
Ransomware accounted for 24% of cybersecurity incidents analyzed by Verizon. The company saw the number of ransomware attacks being higher in the past two years than in the previous five years combined.
The report also reveals that the human element was involved in approximately three-quarters of the analyzed breaches.
Many of these attacks involved social engineering. This technique can be very useful to attackers in business email compromise (BEC) campaigns, which have more than doubled since the previous year and accounted for over half of incidents involving social engineering.
“Senior leadership represents a growing cybersecurity threat for many organizations,” said Chris Novak, managing director of cybersecurity consulting at Verizon Business. “Not only do they possess an organization’s most sensitive information, they are often among the least protected, as many organizations make security protocol exceptions for them. With the growth and increasing sophistication of social engineering, organizations must enhance the protection of their senior leadership now to avoid expensive system intrusions.”
The report also shows that stolen credentials were leveraged in nearly half of breaches for initial access to an organization’s systems, followed by phishing (12%) and vulnerability exploitation (5%).
In terms of motivation, 95% of attacks observed in the past year were financially motivated, with espionage being the goal in only a small percentage of attacks.
The full Verizon 2023 Data Breach Investigations Report is available in PDF format.
Related: Mandiant 2023 M-Trends Report Provides Factual Analysis of Emerging Threat Trends
Related: Verizon DBIR 2021: Ransomware, Web App and Phishing Attacks Dominate