Travel search website Skyscanner announced on Wednesday the launch of a public bug bounty program with rewards of up to $2,000 per vulnerability.
Skyscanner has been running a private bug bounty program, which it claims helped address over 200 vulnerabilities in its systems. The company has now decided to open its program to the public.
The bug bounty program, run with the help of crowdsourced security platform Bugcrowd, covers the skyscanner.net website and regional domains, the gateway.skyscanner.net API, the iOS and Android apps, and the partnerportal.skyscanner.net website. Other subdomains are out of scope.
The company is particularly interested in vulnerabilities affecting the profile, booking and partner portal sections of its service, but instructed researchers to use test accounts and warned them not to modify or access any user data.
The highest rewards, between $1,500 and $2,000 per vulnerability, have been offered for serious server security misconfigurations, server-side injection flaws, broken authentication issues, sensitive data exposure, and cryptography-related problems.
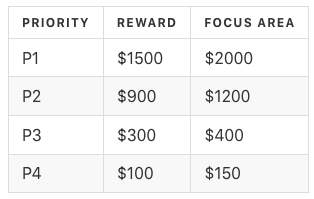
“It is important to note that in some cases a vulnerability priority will be modified due to its likelihood or impact. In any instance where an issue is downgraded, a full, detailed explanation will be provided to the researcher – along with the opportunity to appeal, and make a case for a higher priority,” Skyscanner noted.
All hacking activities must include a special header, they must be conducted using test accounts, and testing must be limited to in-scope assets. Researchers risk a 10% penalty if their submission is valid, but the rules haven’t been followed, Skyscanner said.
Related: Grammarly Launches Public Bug Bounty Program
Related: GitLab Launches Public Bug Bounty Program
Related: Singapore Government Announces Second Bug Bounty Program












