In the cat-and-mouse game between security providers and malware authors, cybercriminals keep innovating and experimenting – a dynamic seen in the recent resurgence of the Locky ransomware.
From a security perspective, 2016 was certainly “The Year of Locky.” In one single day last year, our systems caught 37 billion Locky emails, dwarfing the size of other malware campaigns. But Locky went quiet at the beginning of 2017, and aside from a brief revival here and there, it slipped from the conversation.
But – voila! – August arrived, and Locky experienced a major resurgence, which continues to this day. There’s a small, instructive story there – or at least a theory of mine – which shines a light on the Darwinism of the “malware marketplace.”
Wasn’t Jaff the “New Locky?”
Earlier this year I was trying to figure out why Locky stopped – it had been tremendously successful. Then along came the Jaff ransomware in May. Aha! Jaff is widely understood to be from the same cybercriminal gang behind Locky and the Dridex banking trojan (among others), and it seemed to hold answers to Locky’s mysterious disappearance.
To provide a quick background on Jaff – it came to full active life the same week as the headline-grabbing WannaCry. Many may have missed it, but my security lab team and I were certainly aware of it – in fact, the day before WannaCry took off (May 12), our security cloud caught 65 million Jaff ransomware emails delivered by the Necurs botnet. But because of the impact of WannaCry, Jaff got little attention outside of the security lab community.
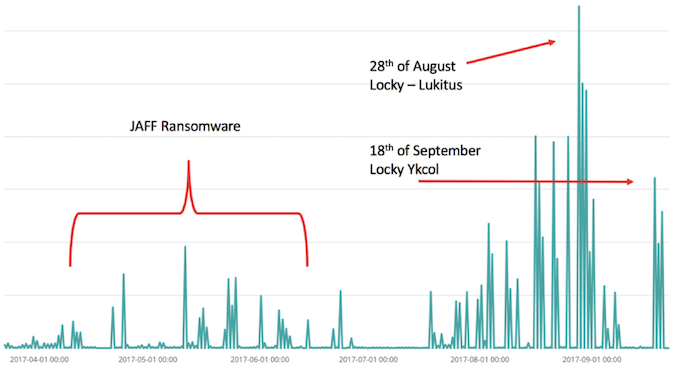
Attack email campaign patterns for Jaff and Locky
Given the fact that Jaff was being distributed by the same botnet as Locky, it made sense that Jaff had perhaps replaced Locky, or at least become the favored weapon. It appeared to be a new, improved Locky in many ways – we even referred to it as “Locky 2,” and speculated amidst the WannaCry outbreak that it might be the more concerning ransomware to watch.
An Upmarket Locky
Looking at Jaff, we hypothesized that the Locky cybergang was innovating further and looking to go “upmarket,” both financially and technically. Jaff was asking for a much higher ransom, on the order of 1.7 Bitcoins ($3,800 at the time), compared to the typical $300-600.
Its programming also represented a leap in sophistication, and it had more moving parts than Locky. Jaff’s chosen payload attachment was more complex than Locky, as it was a PDF that had a .docm (Word document with a macro inside) embedded in the code. And when the macro ran, it would download some JavaScript, and the JavaScript would then download the actual ransomware .exe that encrypts the files. (Whew!)
And the tactics built into Jaff to evade detection were more sophisticated, too, varying all parts of the multi-step attack during each wave to make detection more difficult. The names of the files and the email subjects were randomized, and Jaff reordered the sequence of actions taken by the PDF. At the same time, the Word macro, which set up the download link and downloaded files, was different in every variant; the download links themselves changed. Looking at this malware, we considered it a state-of-the-art cyberattack that maximized the use of sophisticated evasion and obfuscation techniques.
Improving What Works, Killing What Doesn’t
This is where the expected storyline takes a turn. Instead of Jaff taking the world by storm, it has relatively disappeared. Not only that, in the past two months Locky has reemerged with new, improved variants: Diablo, Lukitus (Finnish for “Locking”), and the latest, Ykcol (Locky spelled backwards), which began on September 18 – Cyren’s security cloud saw over 60 million .ykcol e-mails that day delivered by Necurs, and has detected 15,000 different, unique samples of .lukitus sent in a single day.
A theory is that Locky is back because Jaff proved too complex, and the cybergang behind the two decided to go back and upgrade the prior proven and simpler model, rather than insist on their new platform. There are several possible reasons for this – perhaps because the complexity of maintaining and varying a three-level structure (PDF, docm, JavaScript) proved too much work; perhaps they discovered that many moving parts facilitated detection; or perhaps the complexity ended up reducing the “attach” rate of successful infections.
With the disappearance of Jaff, the cybercriminals behind Locky have gone upmarket in one respect – the ransom required is up significantly, to 0.5 BTC or around $2,000 USD per computer today to receive the tool, a multiple of last year’s ransom.
Related: Necurs Botnet Distributing Locky Ransomware via Fake Invoices
















