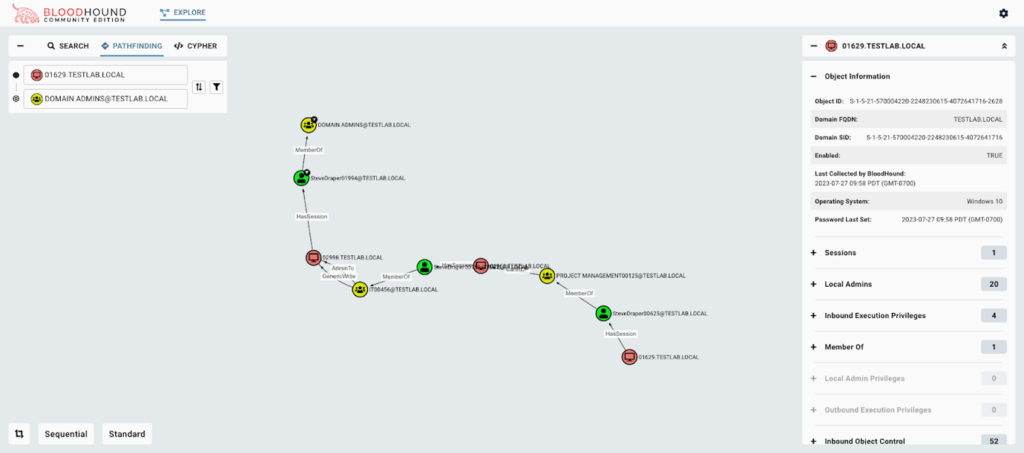
BloodHound is SpecterOps’ graph-based map of Active Directory relationships used by external pentesters (and malicious attackers), and internal users to discover potential lateral movement attack paths from a possibly low-privileged user to a high-privileged domain admin account.
The Active Directory (AD) identity repository is ubiquitous. It is thought that between 90% and 95% of all companies use it. An identity repository for every user’s different access authorizations can get very complex. Complexity can cause misconfigurations, and misconfigurations provide opportunities for attackers. Too much privilege to the wrong user can open a path through AD toward the company’s prized assets, starting from a simple successful phishing attack. This ubiquity and complexity makes Active Directory a highly prized target for attackers.
SpecterOps provides adversary-based cybersecurity solutions with a focus on red teaming and penetration testing. BloodHound Community Edition is its free and open source penetration tool designed to find the AD misconfigurations that could be abused by attackers. SpecterOps has announced version 5.0, which will be available from August 8, 2023.
The original BloodHound was developed in 2016. It provides a graph database map of all the relationships within an AD, showing the connections and potential lateral movement attack opportunities. A sister product, BloodHound Enterprise, was developed for defenders, but with a different code base and released in 2019.
The original BloodHound released in 2016, comments Justin Kohler, VP products at SpecterOps, “is very powerful, but it’s a pain to use. It’s slow. It’s really hard to deploy. It can take hours and there’s some 30 steps that you need to go through. It’s a painful process easily handled by pentesters, but not so simple for internal users.”
This was not suitable for an enterprise version, so although the purpose is similar, the code was rewritten for BH Enterprise release of 2019. “It’s just easier and better and faster and built by actual software engineers versus consultants that did it in their spare time,” said Kohler.
Version 5.0 moves the lessons learned from Enterprise into Community, and vice versa. Importantly, both versions now use the same code base, making future improvements easier, and support faster and more effective. “With this improved efficiency, we expect the release cadence for BloodHound CE to increase dramatically,” comments an associated SpecterOps blog. Noticeably, Kohler commented, “We know there are things not in this new version that the open source community values – minor things like individual widgets here and there – that we fully intend on putting into the future releases already planned.”
Kohler cites two primary drivers for the new BloodHound Community. Firstly, it ‘gives back’ to the open source community. “There’s a 99% reduction in deployment time, and a vast improvement in the time to get results,” he said. The 30 steps needed for deployment have been reduced to one step.
There are further improvements to user management with role based access control, MFA, and SAML support for single sign-on – making it a more secure product for companies running it internally. “Now it’s a traditional enterprise three layer application with an API layer, a UI layer, and the database layer. So, people have API access.,” he added.
The second driver is to enable faster future development across both the Enterprise and Community versions. “Before this update, the two versions used a separate code base,” said Kohler. “This required a duplication of effort – if we built a feature here, we also needed to build it there. The single code base unifies upgrades and allows faster updates from our engineering team.”
Andy Robbins, co-creator of BloodHound, summarized, “Our commitment to the BloodHound community and the goals of the project remain the same: helping penetration testers and defenders uncover the hidden, unintentional, and exploitable relationships in Active Directory. This update allows us to strengthen both products by applying two years’ worth of knowledge gained from building BloodHound Enterprise to BloodHound Community, and by bringing some in-demand features from Community into Enterprise at the same time. BloodHound Community is the same BloodHound that long time open-source users know and love, now with enterprise-grade deployment, usability, and UI.”
In July 2023, Seattle-based SpecterOps extended a Series A funding round, adding a further $8.5 million to the earlier £25 million announced in April 2023.
Related: In the Hacker’s Crosshairs: Active Directory
Related: Black Basta Ransomware Linked to FIN7 Cybercrime Group
Related: Cyberattack Victims Often Attacked by Multiple Adversaries: Research
Related: Samas Ransomware Uses Active Directory to Infect Entire Networks











