Researchers have discovered many vulnerabilities in over a dozen small office/home office (SOHO) routers and network-attached storage (NAS) devices as part of a project dubbed SOHOpelessly Broken 2.0.
The first SOHOpelessly Broken project started in 2013, when researchers at Independent Security Evaluators (ISE) analyzed several SOHO routers and NAS devices. That project resulted in the discovery of many new vulnerabilities to which 52 CVE identifiers were assigned at the time.
ISE last year decided to conduct another similar assessment to see if and how much IoT security has evolved since then. A total of 13 routers and NAS devices were analyzed as part of the SOHOpelessly Broken 2.0 project, which led to 125 CVEs being assigned to the new vulnerabilities. Results of the research were made public on Monday.
SOHOpelessly Broken 2.0 targeted devices from Buffalo, Synology, TerraMaster, Zyxel, Drobo, ASUS and its subsidiary Asustor, Seagate, QNAP, Lenovo, Netgear, Xiaomi, and Zioncom (TOTOLINK).
The researchers said they identified at least one vulnerability that allowed remote shell access or access to the admin interface in each of the tested products, including cross-site scripting (XSS), OS command injection and SQL injection bugs.
Six of the products were found to have vulnerabilities that can be exploited to gain complete control over a device remotely and without authentication. These products are Asustor AS-602T, Buffalo TeraStation TS5600D1206, TerraMaster F2-420, Drobo 5N2, Netgear Nighthawk R9000, and TOTOLINK A3002RU.
The findings were reported to vendors and most of them promptly responded. The experts said they had some communication issues with Netgear, while Drobo, Buffalo and Zioncom have not responded. It’s worth noting that Buffalo, TerraMaster, Drobo, Zyxel, TOTOLINK and Asustor don’t have vulnerability disclosure programs.
Researchers have determined that newer IoT devices — compared to the findings of the initial SOHOpelessly Broken project — may have some useful security mechanisms in place, such as ASLR, anti-reverse engineering protections, and integrity verification mechanisms for HTTP requests. However, the experts found that many devices still lack basic web application protection systems, such as CSRF tokens and browser security headers, which would have prevented many of the exploits.
“Through SOHOpelessly Broken 2.0, we have shown how the current security controls of IoT vendors do not prevent remote attackers from fully compromising a targeted device. While some of the models required a higher-level of effort to discover the issues, many can be easily exploited by anyone with network-level access to the device. With these results, we can conclude that common devices that are deployed in small office and home office environments are likely vulnerable to exploits that can result in severe damage–despite the increased attention to security that IoT device manufacturers have given since 2013,” the researchers said.
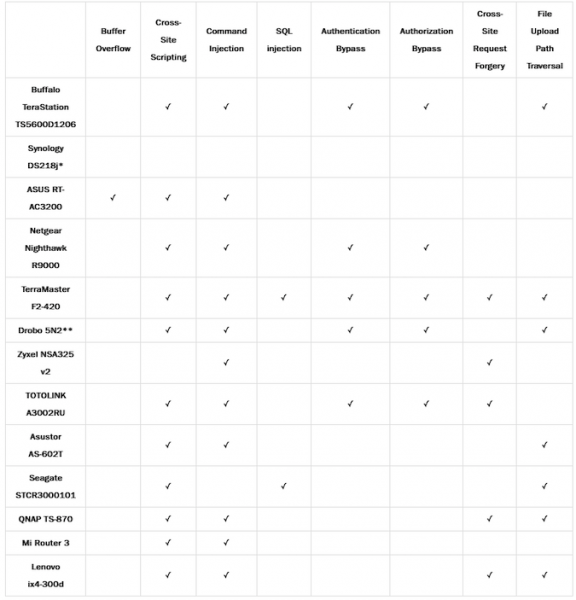
* The issues we reported to Synology (Session Fixation and the ability to Query Existence of Arbitrary Files) were included in this table.
** Though the Drobo does not include a web application by default, we include vulnerabilities that appear in its optional web application here.
Related: DoS Vulnerabilities Patched in NETGEAR N300 Routers
Related: Thousands of Legacy Lenovo Storage Devices Exposed Millions of Files
Related: Authentication Bypass Vulnerability Found in SoftNAS Cloud















