The number of vulnerabilities discovered in industrial control systems (ICS) continues to increase, and many of them have a ‘critical’ or ‘high’ severity rating, according to a new report from industrial cybersecurity firm SynSaber.
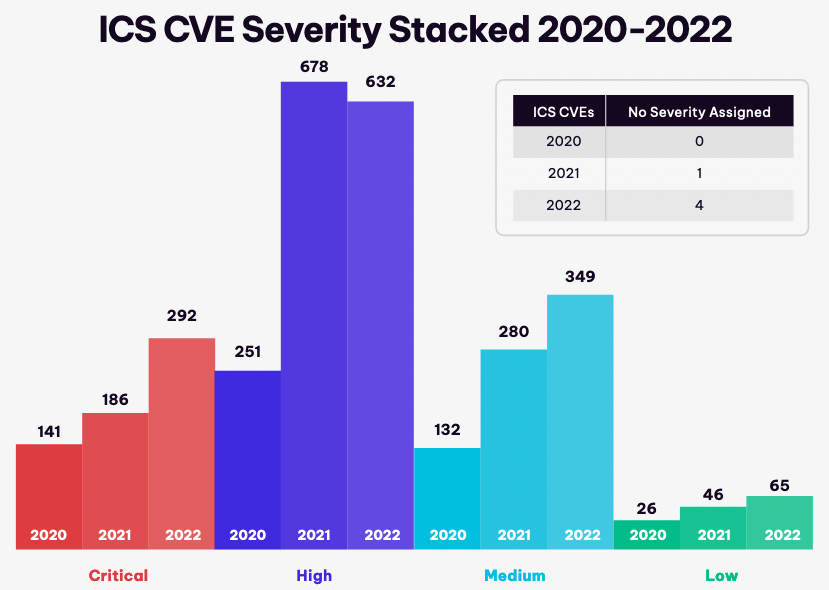
The report compares the number of ICS and ICS medical advisories published by CISA between 2020 and 2022. While the number of advisories was roughly the same in 2021 and 2022, at 350, the number of vulnerabilities discovered last year reached 1,342, compared to 1,191 in the previous year.
The number of vulnerabilities rated ‘critical’ has increased even more significantly, from 186 in 2021 to nearly 300 in 2022. In total, nearly 1,000 vulnerabilities are ‘critical’ or ‘high severity’ based on their CVSS score.
While CVSS scores can be misleading in the case of ICS flaws and they should not be used on their own for patching prioritization, these scores can still be useful for ranking issues that meet an organization’s applicability criteria.
Synsaber’s report shows that Siemens stands out when it comes to ICS vulnerability volume. Not only do many of the security holes discovered in 2022 impact Siemens products, the German industrial giant is also responsible for self-reporting the highest number of vulnerabilities, far more than other vendors.
Siemens’ product security team reported 544 vulnerabilities in 2022, up from 230 in the previous year. The second vendor is Hitachi, with 64 bugs.
“The team at Siemens product security continues to increase its reporting cadence with significant year-over-year growth of nearly 3x. While this does inflate the number of known CVEs that affect Siemens product lines compared to others, this should not be viewed as Siemens products being less secure. On the contrary, a mature and repeatable OEM self-reporting process is something all other OEMs should strive to achieve,” SynSaber noted.
Siemens typically addresses dozens of vulnerabilities every month, but many affect third-party components used by the company’s products.
While the number of vulnerabilities discovered last year is high, nearly one-third require user interaction for successful exploitation and roughly one-quarter require local or physical access to the targeted system. It’s worth noting, however, that the percentage of flaws requiring user interaction and local access has decreased compared to 2021.
Looking at the data for the past three years, one worrying aspect is that the number of ‘forever-day vulnerabilities’ — these are flaws that will likely never get patches — increased to 28% in 2022, up from 14% in 2021.
ICS vulnerabilities can impact software, firmware or protocols. The percentage of issues found in each of these categories has been fairly constant in 2020-2022, with software accounting for 56%, firmware for 36% and protocols for 8%, on average over the three years.
Related: 2023 ICS Patch Tuesday Debuts With 12 Security Advisories From Siemens, Schneider
Related: SynSaber Launches Palm-Sized Threat Sensor for OT Environments














