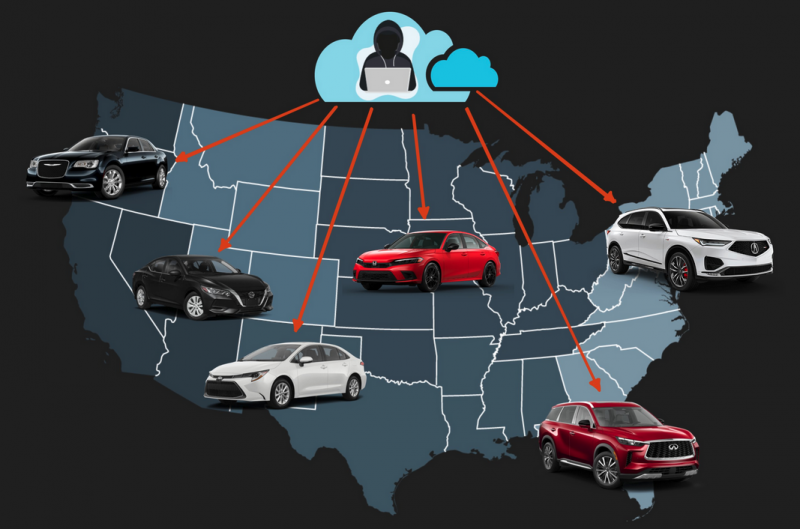
Cybersecurity researchers discovered that several car brands were exposed to remote hacker attacks due to a vulnerability in a connected vehicle service provided by a subsidiary of satellite radio company Sirius XM.
Sirius XM Connected Vehicle Services claims on its website that its connected services are used by more than 12 million vehicles in North America, including Acura, BMW, Honda, Hyundai, Infiniti, Jaguar, Land Rover, Lexus, Nissan, Subaru, and Toyota cars.
Researcher Sam Curry on Wednesday described a recent car hacking project targeting Sirius XM Connected Vehicle Services, which he and his team learned about when looking for a telematic solution shared by multiple car brands.
An analysis led to the discovery of a domain used when enrolling vehicles in the Sirius XM remote management functionality, Curry said in a Twitter thread.
Initial tests were conducted on the NissanConnect mobile application, which led to the discovery of a vulnerability that could allow a remote hacker to obtain a vehicle owner’s name, phone, number, address and car details simply by knowing their VIN, which is typically visible on the windshield. The attacker would need to send specially crafted HTTP requests containing the victim’s VIN in a certain parameter.
Further analysis showed that the same vulnerability could be exploited to run vehicle commands, including locate, unlock and start a car, as well as to flash headlights and honk the horn.
[ READ: Automotive Security Threats Are More Critical Than Ever ]
The researchers determined that such an attack could be launched against Honda, Nissan, Infiniti, and Acura cars.
Sirius XM immediately patched the vulnerability after being informed of its existence. The company said it released a patch within 24 hours and noted that it has no evidence of any data getting compromised or unauthorized modifications being made.
In a separate Twitter thread this week, Curry reported a different vulnerability, one that allowed researchers to control some functions of Hyundai and Genesis vehicles — including locks, engine, horn, headlights and trunk — by knowing the email address the victim had used to register a user account.
The attack allegedly worked on vehicles made after 2012. Hyundai and Genesis also released patches after being notified.
“Hyundai worked diligently with third-party consultants to investigate the purported vulnerability as soon as the researchers brought it to our attention,” Hyundai told SecurityWeek in a statement. “Importantly, other than the Hyundai vehicles and accounts belonging to the researchers themselves, our investigation indicated that no customer vehicles or accounts – for either Hyundai or Genesis – were accessed by others as a result of the issues raised by the researchers.”
“We also note that in order to employ the purported vulnerability, the e-mail address associated with the specific Hyundai/Genesis account and vehicle as well as the specific web-script employed by the researchers were required to be known. Nevertheless, Hyundai and Genesis implemented countermeasures within days of notification to further enhance the safety and security of our systems,” the carmaker added. “Separately, Hyundai and Genesis were not affected by a Sirius XM authorization flaw that was recently disclosed.”
*updated with statement from Hyundai
Related: Researchers Hack Remote Keyless System of Honda Vehicles
Related: Honda Admits Hackers Could Unlock Car Doors, Start Engines
Related: Tesla Car Hacked Remotely From Drone via Zero-Click Exploit














