Several cybersecurity firms have warned Microsoft that cybercriminals have been using signed malicious drivers to kill processes associated with antivirus (AV) and endpoint detection and response (EDR) products.
Alongside its Patch Tuesday updates for December 2022, Microsoft issued an advisory to inform customers about drivers certified by its Windows Hardware Developer Program being used by threat actors in post-exploitation activity, including the deployment of ransomware.
“Microsoft has completed its investigation and determined that the activity was limited to the abuse of several developer program accounts and that no compromise has been identified. We’ve suspended the partners’ seller accounts and implemented blocking detections to help protect customers from this threat,” the tech giant said.
“This investigation revealed that several developer accounts for the Microsoft Partner Center were engaged in submitting malicious drivers to obtain a Microsoft signature,” it added.
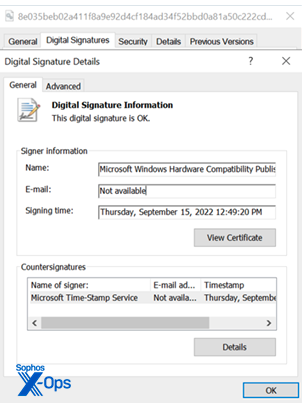
In addition to suspending the accounts, Microsoft has released Windows security updates to revoke the abused certificates.
[ Read: Microsoft Plugs Windows Hole Exploited in Ransomware Attacks ]
The company learned about the abuse from SentinelOne, Mandiant and Sophos. Each company published a blog post on Tuesday to describe its findings.
SentinelOne reported seeing several attacks where a threat actor used malicious signed drivers to evade security products, which typically trust components signed by Microsoft.
The security firm saw threat actors targeting organizations in the business process outsourcing (BPO), telecommunications, entertainment, transportation, MSSP, financial and cryptocurrency sectors. In some cases, the goal was to conduct SIM swapping.
This description is similar to CrowdStrike’s recent description of a cybercrime group tracked as Scattered Spider, which targeted the same industries and had similar goals.
SentinelOne has also seen signed drivers being used to deploy the Hive ransomware against an organization in the medical industry.
The company has analyzed a small toolkit designed to terminate AV and EDR processes. The toolkit has two main components: a userland component called StoneStop and a kernel mode component called PoorTry. PoorTry is a malicious driver that has been signed by hackers, and StoneStop is its loader.
Mandiant has seen this toolkit being used by a financially motivated threat group it tracks as UNC3944, which has been active since at least May and has been using stolen credentials obtained from SMS phishing operations to gain initial access to targeted networks.
Mandiant has observed several distinct malware families, associated with different threat actors, abusing the same process to get their drivers signed by Microsoft.
One of them appears to be the Cuba ransomware, which has been linked by Sophos to attacks leveraging signed drivers to disable cybersecurity products. The group behind the Cuba operation has used a utility called BurntCigar to disable endpoint protection products. BurntCigar was initially signed with stolen certificates, then with valid certificates of shady origin, and then with legitimate Microsoft certificates.
Coinciding with the alerts from Microsoft and cybersecurity firms, the US Cybersecurity and Infrastructure Security Agency (CISA) has updated its alert on the Cuba ransomware with additional indicators of compromise (IoCs).
This is not the first time threat actors have used drivers signed by Microsoft in their operations and it seems that putting a stop to this practice has not been an easy task for Microsoft, which said on Tuesday that it’s taking steps to address the issue.
Both SentinelOne and Mandiant believe the malicious signed drivers may be provided to different threat actors by one or more suppliers that specialize in offering these types of services. SentinelOne noted that this theory is supported by the similar functionality and design of drivers used by different threat groups.
Related: North Korean Hackers Exploit Dell Driver Vulnerability to Disable Windows Security
Related: Ransomware Operator Abuses Anti-Cheat Driver to Disable Antiviruses















