A threat actor tracked as ‘Scattered Spider’ is targeting telecommunications and business process outsourcing (BPO) companies in an effort to gain access to mobile carrier networks and perform SIM swapping, cybersecurity firm CrowdStrike warns.
A financially-motivated threat actor, Scattered Spider has been observed increasingly targeting the telecoms industry since June 2022, setting up persistence mechanisms and even reverting implemented mitigations to regain access to the compromised networks.
According to CrowdStrike, Scattered Spider has been relentlessly trying to gain access to victim networks, typically performing daily operations once access has been obtained. The threat actor was seen deploying virtual private network (VPN) and remote monitoring and management (RMM) tools.
The cybersecurity firm explains that, after successfully containing Scattered Spider’s intrusion into one organization, the threat actor moved to a different company in the same vertical, using the same tactics, techniques and procedures (TTPs).
“In all observed intrusions, the adversary attempted to leverage access to mobile carrier networks from a Telco or BPO environment, and in two investigations, SIM swapping was performed by the adversary,” CrowdStrike notes.
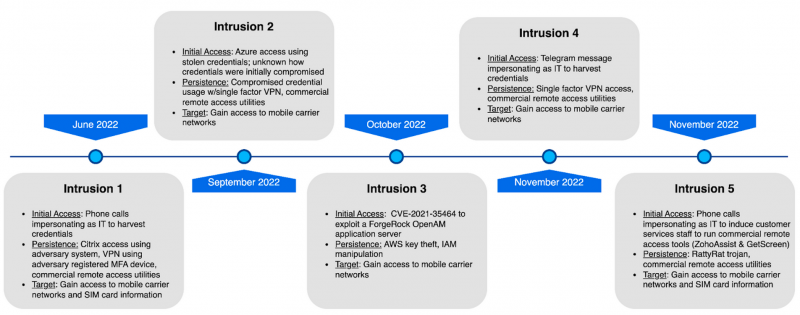
For initial access, the threat actor leveraged social engineering, including via phone calls and SMS and Telegram messages impersonating IT staff, to trick victims into entering their credentials on a phishing page, or downloading and installing a RMM tool controlled by the attackers.
Scattered Spider would also engage with the victims directly to obtain their one-time password (OTP) if multi-factor authentication (MFA) was enabled, or relied on MFA push-notification fatigue for that.
In one attack, the adversary used compromised credentials to access a victim’s Azure tenant and instantiate Azure VMs for credential theft and lateral movement.
The threat actor was also observed exploiting CVE-2021-35464, a critical flaw in the ForgeRock Access Management (AM) solution that can lead to code execution. ForgeRock’s OpenAM application server front-ends web applications in many organizations.
In many cases, the attackers gained access to the victim organization’s MFA console to add their own devices and assign them to user accounts they had compromised credentials for, thus being able to maintain a deep level of persistence.
The use of a broad range of legitimate RMM tools also helped the attackers fly under the radar and avoid being blocked by endpoint detection and response (EDR) solutions.
The threat actor was also seen using various ISP and VPN providers to access the victim organizations’ Google Workspace environments, Azure AD, and on-premises infrastructure (targeting both Windows and Linux systems). In one attack, the attackers downloaded Azure AD group members and users in bulk.
“In all investigations performed by CrowdStrike incident responders, the faster the organization implemented swift and bold security measures, the faster the adversary activity ceased. These containment and mitigation measures focused on secure identity and MFA controls and configurations,” CrowdStrike explains.
Related: Chinese Hackers Target Europe, Tibetans With ‘Sepulcher’ Malware
Related: CrowdStrike: Ransomware Actor Caught Exploiting Mitel VOIP Zero-Day
Related: Sophisticated Threat Actor Targets Governments, Defense Industry in Western Asia















