Salt Security emerged from stealth mode on Tuesday with a solution designed to identify and prevent API attacks, and $10 million in funding.
Application programming interfaces (APIs) have been involved in several high profile security incidents in the past years and an increasing number of companies have started offering API protection solutions.
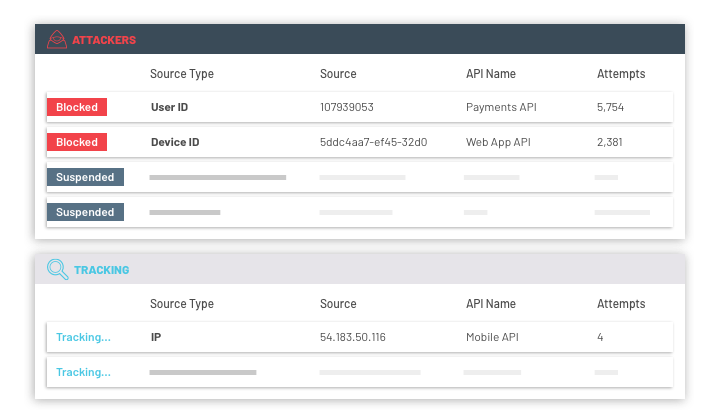
 Salt Security claims that solutions from other vendors can only detect known API attacks, but its own AI-powered technology can spot anomalies in real time and block threats in the reconnaissance phase.
Salt Security claims that solutions from other vendors can only detect known API attacks, but its own AI-powered technology can spot anomalies in real time and block threats in the reconnaissance phase.
The company says it can provide an inventory of all APIs within hours and helps organizations assess the risks associated with each component. Its solution should be able to detect zero-day attacks by creating a profile of legitimate APIs.
Salt also helps customers identify insecure APIs and provides information on how these weak spots can be remediated in minutes, the company claims.
Salt says its API Protection Platform, which is available in a software-as-a-service (SaaS) or a hybrid deployment if on-premises data processing is required, can be deployed in a matter of minutes without requiring any code changes from the development team.
The firm says its platform has already been used by “numerous” enterprise customers.
“Customers tell us they are using our global cloud database, MongoDB Atlas, for the peace of mind that comes with secure, managed data working in concert with the scalability and convenience of APIs,” said Davi Ottenheimer, head of product security at MongoDB. “Salt presents a new approach to addressing current and future threats, whether around big data, Internet of Things, microservices or machine learning applications, and we are very excited to explore enhanced API security with them.”
S Capital, Lookout co-founder and Y-Combinator expert Kevin Mahaffey, and Marius Nacht, co-founder and chairman of Check Point, took part in the funding round. The newly acquired funds will be used to increase R&D for Salt Security’s core platform and add support for new use cases in response to growing customer demand.
Related: Ping Identity Acquires API Security Firm Elastic Beam
Related: Elastic Beam Emerges From Stealth With API Security Solution
Related: Leaked GitHub API Token Exposed Homebrew Software Repositories














