Redwood City, Calif.-based Elastic Beam emerged from stealth mode on Wednesday with the launch of a security solution designed to detect and block cyberattacks targeting application programming interfaces (APIs).
The company’s flagship product, API Behavioral Security (ABS), is an engine that uses artificial intelligence (AI) to detect threats in real time. Data from ABS is sent to the API Security Enforcer (ASE) to block the attack and prevent the attacker from reconnecting.
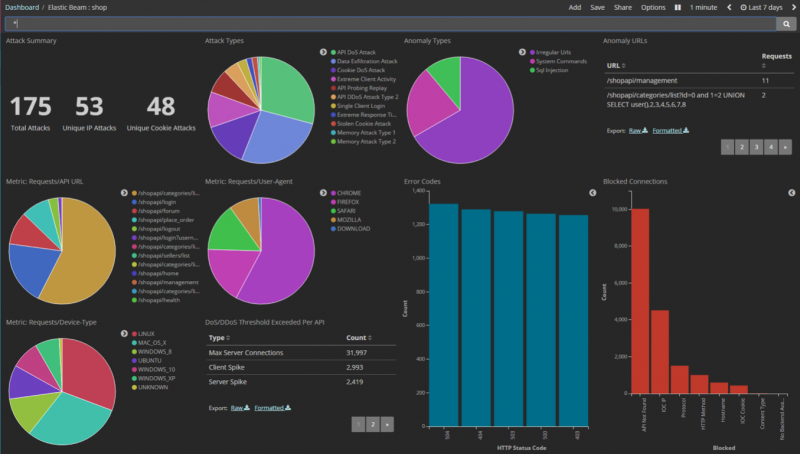
According to Elastic Beam, its solution can detect data exfiltration, unauthorized changes or removal of data, distributed denial-of-service (DDoS) attacks, code injections, brute force attempts and authentication via stolen credentials, API memory attacks, WebSocket attacks and other types of external and insider threats.
The product, designed for API gateways, API management platforms and app servers, works in both public and hybrid cloud environments and on premises. The vendor says it also has the ability to scale automatically using elastic clustering.
“We look at the whole traffic pattern between the end-point/client and the system being accessed,” Bernard Harguindeguy, founder and CEO of Elastic Beam, told SecurityWeek. “We implemented AI algorithms that combine advanced AI techniques with our strong API behavior and security expertise to automatically sort out sessions that are not normal.”
“The system does not use predefined policies or security rules, it is self-learning, and uses the AI engine to continuously update knowledge of the environment and traffic. It uses much more than a traditional baseline to identify an attack. Also the attacks are identified as such – not just anomalies. So we will flag anomalies if something is ‘off’ but not really an attack – and we will identify an attack when we believe that it is truly an attack,” Harguindeguy explained.
For forensic analysis and reporting purposes, Elastic Beam says its product provides tracking and reporting capabilities for all API activity. The solution also includes a decoy API feature that relies on a deception mechanism to lure hackers and capture attack information for analysis.
The product is available through a subscription pricing model based primarily on API transaction volumes. Elastic Beam, which has so far been funded by its founders and angel investors, says ABS has already been tested in banks, government agencies, cloud services and IoT environments.
Related Reading: RedLock Emerges from Stealth With Cloud Security Platform
Related Reading: Enterprise IoT Security Firm Armis Emerges From Stealth