Security researchers have spotted a brand new ransomware family taking aim at corporate networks, warning that professional cybercriminals have already hit multiple organizations with the file-encryption scheme.
The new ransomware family, called Babuk, has claimed at least four corporate victims facing data recovery extortion attempts.
According to researcher Chuong Dong, the ransomware is pretty standard and lacks obfuscation but he warned that the cybercriminals have found success with the use of strong encryption.
“Despite the amateur coding practices used, its strong encryption scheme that utilizes Elliptic-curve Diffie–Hellman algorithm has proven effective in attacking a lot of companies so far,” Dong explained.
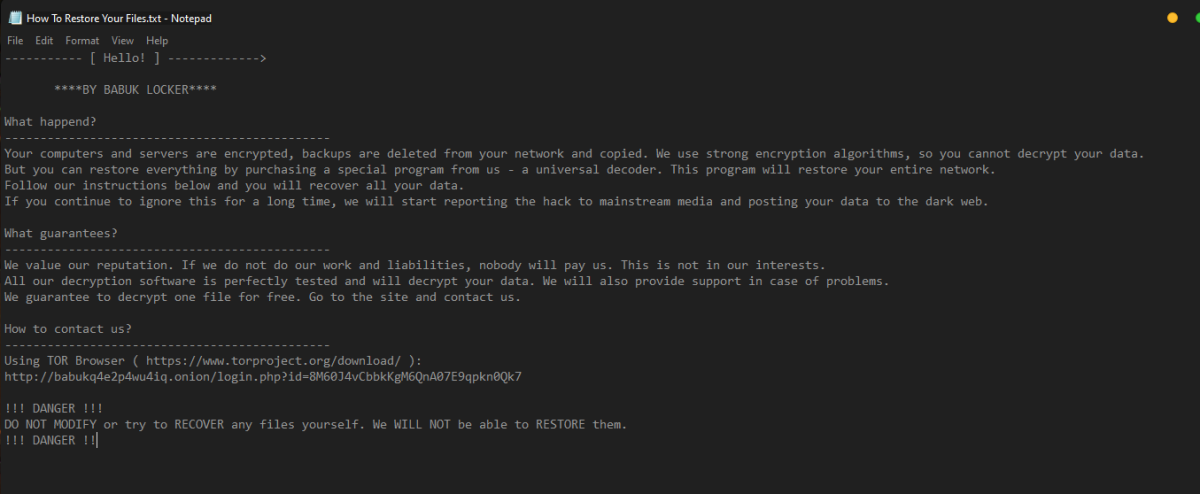
(Click to view full size image. Image credit: Chuong Dong)
Similar to other ransomware families out there, Dong said Babuk uses techniques such as multi-threading encryption. It was also observed abusing the Windows Restart Manager, similar to the Conti and REvil ransomware strains.
Babuk uses a proprietary implementation of ChaCha8 encryption, SHA256 hashing, and Elliptic-curve Diffie–Hellman (ECDH) algorithm for key generation and exchange for securing keys and encrypting files. Furthermore, for each malware sample, the authors use a single private key.
The ransomware only encrypts local machines if no command line parameters are supplied. With parameters, it can either encrypt locally only or move to encrypting network shares after encrypting local machines.
Babuk also includes functionality to close specific services and processes before starting the encryption operation. It targets multiple backup services, as well as processes for database, office applications, browser, and email clients.
It uses Windows Restart Manager to terminate processes, to ensure files can be encrypted, and attempts to delete shadow copies, both before and after the encryption.
The key generation mechanism used by Babuk is rather complex, meant to ensure that the victim can’t recover their files, but allowing the attackers to easily generate the shared secret needed for decryption. The approach to multithreading, however, can be considered mediocre, Dong said.
Related: Ransomware Attacks Linked to Chinese Cyberspies
Related: Ryuk Attacks Continue Following TrickBot Takedown Attempt
Related: Sodinokibi Ransomware Operators Target POS Software