A researcher at privileged access management solutions provider CyberArk has discovered vulnerabilities in the products of 10 cybersecurity vendors.
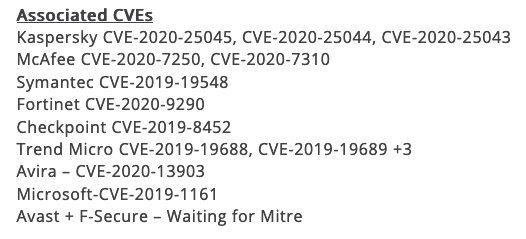
CyberArk researcher Eran Shimony reported this week that he identified flaws in products from Kaspersky (advisory), McAfee, Symantec, Fortinet, Checkpoint, Trend Micro, Avira, Microsoft, Avast and F-Secure. He reported his findings to impacted vendors and they have all released patches.
The research focused on vulnerabilities that can allow an attacker or a piece of malware to escalate privileges using symlink attacks or DLL hijacking. In some cases, the security bugs may have allowed attackers to delete arbitrary files. These types of attacks against antimalware products were also detailed earlier this year by researchers at RACK911 Labs.
A symlink, or symbolic link, is basically a shortcut file. However, researchers have shown on numerous occasions that specially crafted symlinks can be exploited to write, modify or delete files, which can be leveraged to escalate privileges or cause damage to the system.
Shimony has analyzed two types of attack methods involving symlinks: one where a non-privileged process creates files or folders that would later be used by a privileged process, and one where a directory is created by the attacker before it’s created by a privileged process. In both cases an attacker could use symlinks to elevate privileges with the aid of the privileged process.
His blog post demonstrates the first type of attack against an Avira product, and the second attack against a McAfee product. However, he pointed out that products from other vendors are affected as well.
The researcher also found that many antimalware software installers rely on an old installation framework, allowing an attacker to conduct DLL hijacking attacks to escalate privileges.
DLL hijacking vulnerabilities were found in the past in the products of several major companies. These attacks involve an attacker placing a malicious DLL in a location on the targeted system from where it would get executed before a legitimate DLL with the same file name.
DLL hijacking can require elevated privileges, but in the case of installers, they are often executed from the Downloads folder, which can be accessed even by users with lower permissions.
The researcher has also shared some recommendations on how developers can avoid introducing these types of vulnerabilities in their products.
“The implications of these bugs are often full privilege escalation of the local system. Due to the high privilege level of security products, an error in them could help malware to sustain its foothold and cause more damage to the organization. The exploits that were presented here are easy to implement, but also easy to patch against,” Shimony explained. “We have seen that blocking symlink attacks or blocking the load of malicious DLLs require only a small touchup in the code. Knowing that, AV vendors should be able to eliminate this widespread bug class.”
Related: Vulnerability Prompts Avast to Disable Emulator Used by Antivirus
Related: Antivirus Vendors Patch Bug First Discovered 10 Years Ago














