In-the-wild exploitation of a critical vulnerability in JetBrains’ TeamCity continuous integration and continuous deployment (CI/CD) server started just days after the availability of a patch was announced.
The vulnerability, tracked as CVE-2023-42793, impacts the on-premises version of TeamCity and it allows an unauthenticated attacker with access to a targeted server to achieve remote code execution and gain administrative control of the system.
JetBrains announced the release of TeamCity 2023.05.4, which patches the flaw, on September 21.
Sonar, the code security firm whose researchers discovered the issue, released some limited information the same day, and published technical details roughly a week later after a proof-of-concept (PoC) exploit was made public.
Sonar warned in its initial blog post that in-the-wild exploitation would likely be observed soon due to how easily the flaw can be exploited.
Threat intelligence firm GreyNoise started seeing the first exploitation attempts on September 27, with a peak seen the following day. The company has seen attack attempts coming from 56 unique IP addresses as of October 1.
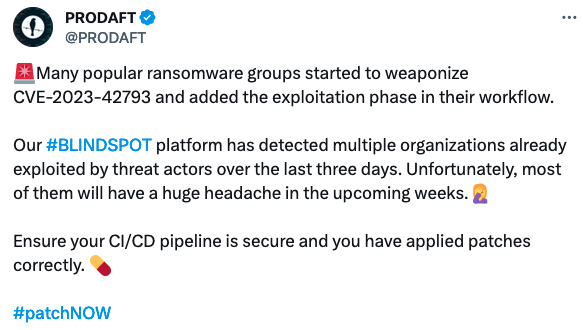
A different threat intelligence company, Prodaft, reported seeing “many popular ransomware groups” targeting CVE-2023-42793.
The Shadowserver Foundation, a non-profit cybersecurity organization, has scanned the internet for vulnerable TeamCity servers and identified nearly 1,300 unique IPs, with the highest percentage located in the United States, followed by Germany, Russia and China.
Organizations using TeamCity should update their installation as soon as possible. For customers who cannot immediately install the update, JetBrains has provided a security patch plugin that can be used to mitigate the issue on servers running TeamCity 8.0 and later. TeamCity Cloud customers do not need to take any action.
Related: CISA Warns of Old JBoss RichFaces Vulnerability Being Exploited in Attacks
Related: Hackers Set Sights on Apache NiFi Flaw That Exposes Many Organizations to Attacks
Related: Progress Software Patches Critical Pre-Auth Flaws in WS_FTP Server Product














