Trend Micro’s Zero Day Initiative (ZDI) on Tuesday announced the targets, prizes and rules for the Pwn2Own Vancouver 2021 hacking competition, a hybrid event scheduled to take place on April 6-8.
Pwn2Own Vancouver typically takes place during the CanSecWest conference in Vancouver, Canada, but due to the coronavirus pandemic, this year’s event will be hybrid — participants can submit their exploits remotely and ZDI staff in Toronto (Canada) and Austin (Texas) will run the exploits. The attempts will be live-streamed on YouTube and Twitch.
The prize pool for Pwn2Own 2021 exceeds $1.5 million in cash and other prizes, including a Tesla Model 3.
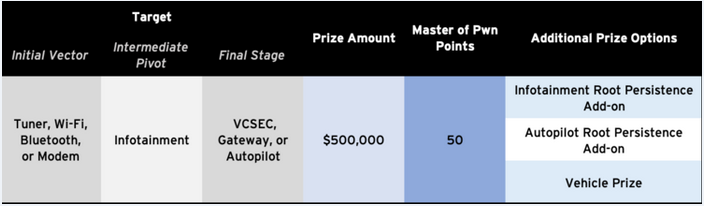
The car is being offered to those who participate in the automotive category. In this category, in addition to the vehicle, hackers can earn up to $600,000 for hacking a Tesla. There are three difficulty levels in this category and the Model 3 is being offered in each of them.
ZDI has also announced a new category for the upcoming event. As part of the new enterprise communications category, participants can earn up to $200,000 for demonstrating exploits against Zoom or Microsoft Teams.
“A successful attempt in this category must compromise the target application by communicating with the contestant. Example communication requests could be audio call, video conference, or message,” ZDI noted.
Other categories include virtualization, with a top prize of $250,000 for Microsoft Hyper-V client exploits, a web browser category, with a top prize of $150,000 for Chrome and Edge exploits, an enterprise application category, with a maximum prize of $100,000 for Microsoft 365 exploits, a server category, with up to $200,000 offered for Microsoft Exchange and Windows RDP exploits, and a local privilege escalation category, with $40,000 being the top prize for Windows 10 exploits.
Registration for the event closes on April 2. The complete rules are available on ZDI’s website.
At last year’s event, the first edition of Pwn2Own affected by the pandemic, white hat hackers only earned a total of $270,000 for their exploits.
Related: Researchers Earn $280,000 for Hacking Industrial Systems at Pwn2Own Miami
Related: Routers, NAS Devices, TVs Hacked at Pwn2Own Tokyo 2020
Related: NETGEAR Router, WD NAS Device Hacked on First Day of Pwn2Own Tokyo 2020
Related: Researchers Hack Windows, Ubuntu, macOS at Pwn2Own 2020













