Over 96% of WordPress Vulnerabilities Disclosed in 2020 Affected Third-Party Code
More than 580 WordPress vulnerabilities were disclosed in 2020, but a vast majority of them impact third-party plugins and themes rather than the WordPress core, according to a new report from website security company Patchstack (formerly WebARX).
The report is based on data from Patchstack’s WordPress vulnerability database, which includes information collected by the company’s internal research team and its bug bounty community, by third-party cybersecurity vendors, and by independent security researchers.
It’s worth noting that the WordPress content management system (CMS) powers more than 40% of the websites on the internet, and users have tens of thousands of plugins at their disposal to implement various features.
An analysis of the vulnerabilities disclosed last year showed that of 582 unique issues, more than 96% actually impacted third-party themes or plugins, many of which are present on millions of websites. More than 470 security bugs were found in plugins and only 22 impacted the WordPress core — the rest affected themes.
Patchstack has analyzed 50,000 WordPress websites and found that they use, on average, 23 third-party plugins, four of which were not updated to the latest version.
“With every additional plugin installed on the website, the risk of being exposed to a potential vulnerability increases. The fact that websites are lagging behind with updates increases the risk even more,” Patchstack wrote in its report.
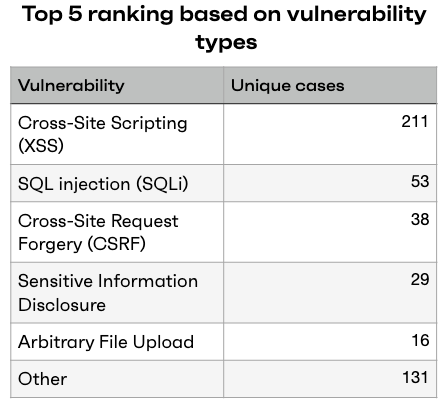
Cross-site scripting (XSS) vulnerabilities were the most common, followed by SQL injection, cross-site request forgery (CSRF), information disclosure, and arbitrary file upload flaws.
Patchstack told SecurityWeek that based on vulnerability reports submitted through its bug bounty program this year, there seems to be an increase in the number of discovered flaws compared to 2020. A survey of 400 developers and digital agencies conducted by the company last year also showed an increase in attacks.
Related: Nearly 1 Million WordPress Sites Targeted via Old Vulnerabilities
Related: Vulnerability That Allows Complete WordPress Site Takeover Exploited in the Wild
Related: Hackers Start Exploiting Recent Vulnerabilities in Thrive Theme WordPress Plugins














