Organizations made some improvements to their security posture last year, but only marginally, as the average time-to-fix is still too high and remediation rates are too low, according to the 12th annual application security statistics report from WhiteHat Security.
WhiteHat Security’s report is based on dynamic and static testing data collected in 2016 from 15,000 web apps and over 65,000 mobile applications.
The figures show a 25 percent improvement in the average number of vulnerabilities found in web applications – the number dropped from four flaws in 2015 to three flaws in 2016. However, the security firm pointed out that a majority of applications have three or more security holes and nearly half of them are critical.
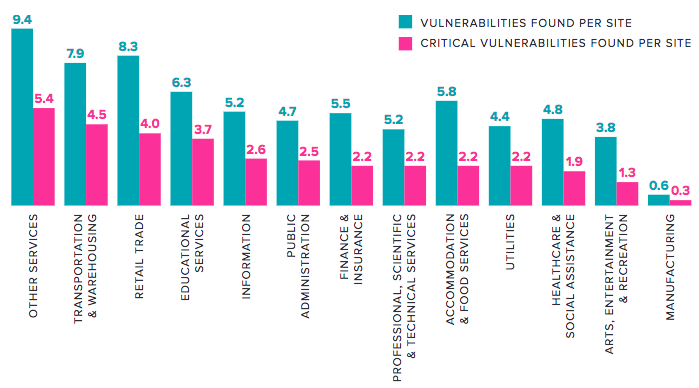
Looking at the vulnerability profile of each industry, we see that the services sector has the highest number of vulnerabilities, followed by transportation, retail and education.
According to WhiteHat, nearly half of the applications it has tested are vulnerable every single day of the year. In industries such as utilities, retail, accommodations and education, roughly 60 percent of web applications are always vulnerable.
Dynamic security testing conducted by the company showed that the most prevalent vulnerabilities are information leakage, cross-site scripting (XSS), content spoofing, and insufficient transport layer protection. The types of vulnerabilities that are most often found to be critical are SQL injection, XSS, cross-site request forgery (CSRF) and insufficient authorization.
While, as expected, development teams focus on fixing critical and high severity flaws first, low-risk weaknesses are addressed before medium-risk ones.
“Development teams are prioritizing critical software problems first, but then move on to easier fixes,” WhiteHat said in its report. “This is human nature. After patching tricky vulnerabilities, why not knock out a few simple ones?”
The study found that while XSS vulnerabilities are critical 40 percent of the time, developers ignored nearly half of these security holes in 2016. Even SQL injection, which is considered critical in 94 percent of cases, only has a remediation rate of 60 percent.
There have been some improvements in the time it takes software developers to fix a vulnerability – the average number of days dropped from 146 days in 2015 to 129 days in 2016. However, it still took developers, on average, nearly 200 days to patch high severity problems, up from 171 in 2015.
Static testing conducted by WhiteHat showed that insufficient transport layer protection, SQL injection, and unpatched libraries are critical in many cases. However, only less than half of critical bugs are fixed in the development process and make it into production.
In the case of vulnerabilities discovered via static testing, developers seem to focus on issues that are easy to fix and often neglect more severe problems.
The full Application Security Statistics Report, which also includes data on mobile application vulnerabilities, is available in PDF format.












