A critical Oracle WebLogic Server vulnerability patched last week has been exploited by malicious actors to deliver a new piece of ransomware to organizations.
The ransomware, named Sodinokibi, is designed to encrypt files and delete backups in an effort to prevent victims from recovering their files without paying a ransom. It has been analyzed by independent researchers, South Korean cybersecurity firm EST Security, Cisco’s Talos research and intelligence group, and others.
Talos researchers were the ones who spotted Sodinokibi being delivered via the recently fixed WebLogic Server flaw. Deploying ransomware via a vulnerability in WebLogic Server can be highly efficient as, unlike in the case of other attack vectors, no user interaction is required.
Oracle WebLogic Server is a Java EE application server that is part of the company’s Fusion Middleware offering. Vulnerabilities affecting this piece of software can be useful to attackers whose campaigns are aimed at enterprises.
According to Talos, the attackers used PowerShell commands to download and execute their malicious files. Talos and others pointed out that the ransomware is designed to allocate a unique alphanumeric extension to encrypted files on each compromised system.
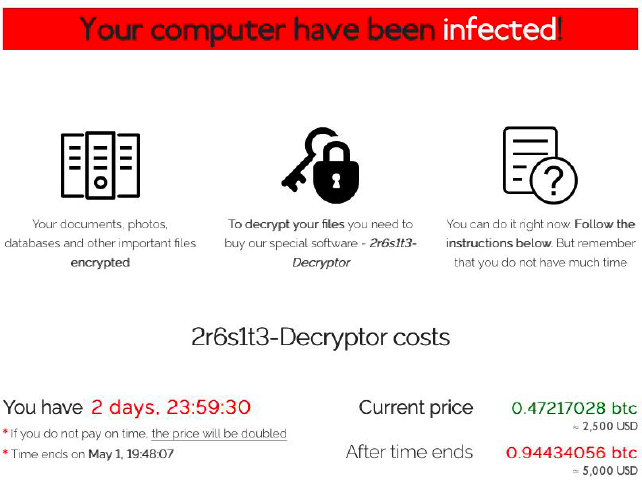
The ransom demanded by the cybercriminals appears to vary. In some cases it’s $1,500 (the equivalent in bitcoin), while in others it’s $2,500. The amount doubles if the ransom is not paid within a specified number of days — some victims were given two days, while others were given six days to pay the ransom before the amount doubled.
One sample uploaded on Tuesday to VirusTotal is detected at the time of writing by 43 of 70 antivirus engines.
The WebLogic Server vulnerability used to deliver the malware is CVE-2019-2725, a critical remote code execution issue. Oracle released an out-of-band update to patch the vulnerability on April 26, after several in-the-wild attacks were observed.
Talos started seeing the first stages of the Sodinokibi attacks — the attackers first looked for exploitable WebLogic servers — on April 25, one day before Oracle released patches.
Talos also noted that in one of the attacks the hackers exploited CVE-2019-2725 once again roughly eight hours after deploying Sodinokibi. This time they leveraged the vulnerability to deliver another piece of ransomware, Gandcrab.
“We find it strange the attackers would choose to distribute additional, different ransomware on the same target. Sodinokibi being a new flavor of ransomware, perhaps the attackers felt their earlier attempts had been unsuccessful and were still looking to cash in by distributing Gandcrab,” Talos researchers explained.
In addition to ransomware, CVE-2019-2725 has been exploited to deliver cryptocurrency miners and other types of malware. Experts believe it has also likely been exploited in targeted attacks.
Related: Oracle WebLogic Server Flaw Exploited to Deliver Crypto-Miners
Related: Hackers Target Poorly Patched Oracle WebLogic Flaw
Related: Recently Patched Oracle WebLogic Flaw Exploited in the Wild













