The US Cybersecurity and Infrastructure Security Agency (CISA) on Wednesday announced the release of a free and open source tool designed to help defenders map attacker behavior to the Mitre ATT&CK framework.
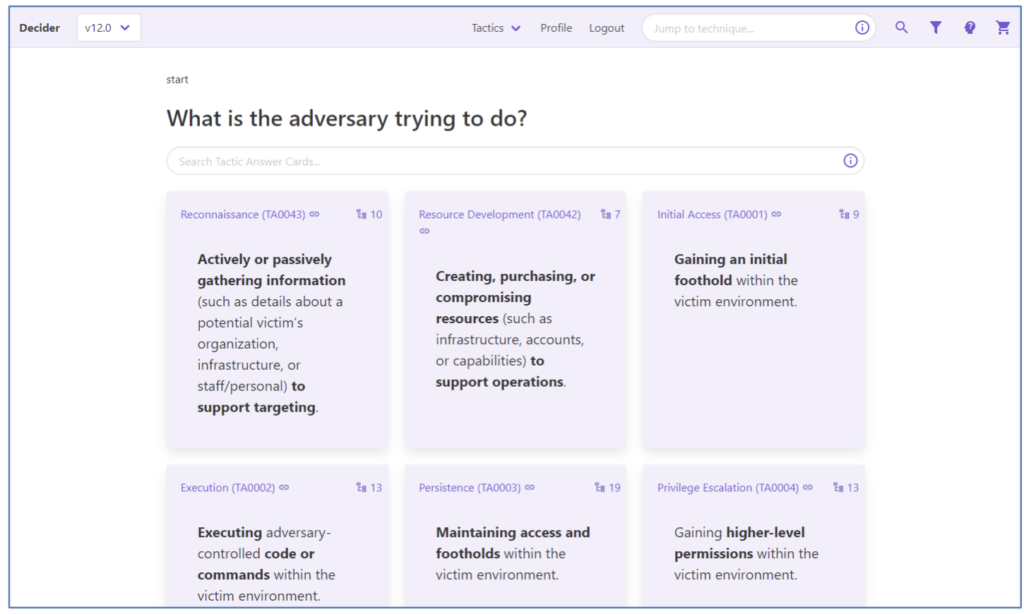
The new tool, named Decider, was developed in partnership with the Homeland Security Systems Engineering and Development Institute (HSSEDI) and Mitre. Decider makes the mapping process easier by asking the user a series of questions about the adversary’s activity in their network.
The tool also provides search and filtering functionality, and allows users to export the results to common formats.
Decider is available on GitHub, but since it’s a web application it must be hosted somewhere before it can be used. CISA has published a fact sheet and a blog post to help defenders get started with Decider.
The Mitre ATT&CK knowledge base of adversary tactics, techniques and procedures (TTPs) has been increasingly used by security professionals to understand adversary behavior. It can be useful for assessing security tools, identifying defense gaps, hunting for threats, and validating mitigation controls.
However, CISA learned that many stakeholders are having difficulties when it comes to mapping hacker behavior to ATT&CK. That is why it has developed Decider.
The tool uses simplified language to guide the user through a decision tree format, helping them pick the correct technique or subtechnique. It also provides information on potentially incorrect mappings and similar techniques to ensure accuracy.
Decider is compatible with Enterprise ATT&CK 11.0 and 12.0.
Related: Google’s GUAC Open Source Tool Centralizes Software Security Metadata
Related: Academics Devise Open Source Tool For Hunting Node.js Security Flaws
Related: New Open Source Tool Shows Code Injected Into Websites by In-App Browsers

