Foreign embassies in Belarus have been targeted by a cyberespionage group that appears to leverage adversary-in-the-middle (AitM) techniques through internet service providers (ISPs) in the country, according to a new report from ESET.
Dubbed MoustachedBouncer, the threat actor has been around since at least 2014 and it has apparently started using AimT attacks in 2020. The group is believed to be operating on behalf of the Belarusian government.
ESET is aware of attacks against the Belarusian embassies of four countries: two in Europe, one in Africa, and one in South Asia.
The security company’s researchers have identified several pieces of malware used by the cyberspies, including ones named NightClub, Disco, and SharpDisco. The malware and their plugins enable the attackers to monitor files and exfiltrate data from compromised systems, including files, screenshots and audio recordings.
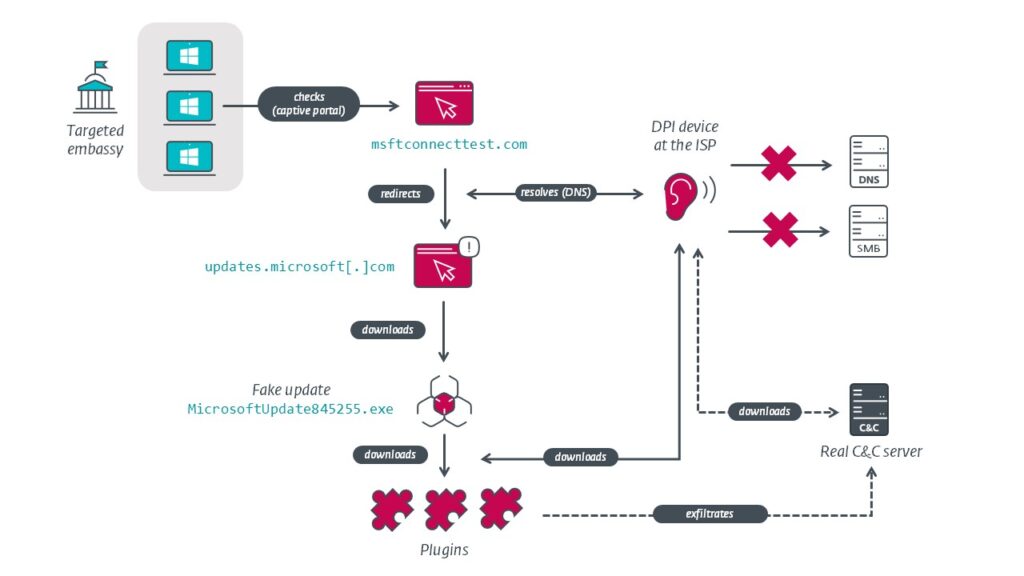
At least some of these malware families are believed to have been delivered using AitM attacks at the ISP level, with the traffic of targeted IP addresses being redirected to a fake Windows update site set up to distribute malware. ESET has named two Belarusian ISPs that may be involved in the operation: Unitary Enterprise A1 and Beltelecom.
The cybersecurity firm has found evidence suggesting that MoustachedBouncer has been collaborating with a Russia-linked group named Winter Vivern, which has targeted government entities in Europe and Asia, including NATO members.
The company believes that Belarusian state-sponsored threat actors are using a lawful surveillance system named System of Operative-Investigative Measures (SORM) to conduct the attacks.
Telecom providers in the country are required by law to ensure that their hardware is compatible with the SORM system, which gives authorities direct access to user communications and associated data without the need to notify the provider.
ESET noted that it cannot completely rule out the possibility that the AitM attacks were launched using compromised routers within the targeted embassies, but these lawful interception capabilities make it more likely that the attacks are being conducted at ISP level.
“The main takeaway is that organizations in foreign countries where the internet cannot be trusted should use an end-to-end encrypted VPN tunnel to a trusted location for all their internet traffic in order to circumvent any network inspection devices,” ESET concluded.
Related: Mandiant Attributes Ghostwriter APT Attacks to Belarus
Related: Russia-Linked APT29 Uses New Malware in Embassy Attacks

