Millions of devices deployed across a wide range of sectors could be exposed to hacker attacks due to security issues associated with the use of LoRaWAN, cybersecurity firm IOActive warned on Tuesday.
LoRaWAN, which stands for long range wide area networking, is a media access control (MAC) protocol that uses LoRa technology to allow low-power devices to wirelessly communicate with internet-connected applications over long distances.
LoRaWAN is inexpensive and a single antenna can be used to cover a large area, such as a city, which has made it highly popular around the world. Smart cities use it for parking, lighting and traffic management systems, and industrial organizations use it to track assets and for various other purposes. The protocol is also used for security systems, smart home products, as well as in the agriculture and healthcare sectors.
The LoRa Alliance, the non-profit organization behind the LoRaWAN standard, says there are currently well over 100 million devices using LoRaWAN all around the world and it estimates that the number will reach 730 million by 2023.
IOActive has analyzed versions 1.0.2 and 1.0.3 of the protocol, which are the most widely used. The latest version is 1.1, which brings several improvements in terms of security, but it will take some time until it’s widely adopted and some of the attack methods identified by the company’s researchers also work against this version due to implementation weaknesses.
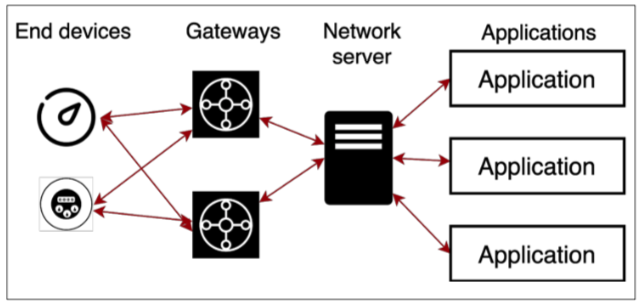
In a LoRaWAN architecture, end devices communicate with applications via gateways and network servers. Devices exchange messages with gateways via LoRa and LoRaWAN, and the gateways communicate with the network server via TCP and UDP. The network servers route traffic from end devices to applications and they are also responsible for authentication and authorization.
LoRaWAN uses network-level security to ensure the authenticity of a device on the network, and application-layer security to prevent access to data exchanged between a device and the application server. These layers rely on secrets called the Network Session Key (NwkSKey) and the Application Session Key (AppSKey) to ensure protection.
LoRaWAN allows two methods for initial device activation and communication with the server: activation by authorization (ABP), which involves hardcoding both session keys and other device identification data in the firmware; and over-the-air activation (OTAA), which involves configuring an AES-128 root key called AppKey that is unique for each device. The AppKey is used to sign the messages exchanged when a device joins a network.
The security of a LoRaWAN network is dependent on these keys being kept safe. Despite the fact that version 1.1 of the protocol introduces significant security enhancements, LoRaWAN systems are often exposed to attacks due to implementation issues and poor key management.
IOActive researchers have found that keys can be extracted from devices through reverse engineering. Many devices also come with tags containing information such as the AppKey. These tags should only be used in the commissioning process, but if they are not removed once the device has been deployed, an attacker who has physical access to the device can use the information from the tag to generate session keys.
Researchers have also uncovered source code that includes hardcoded AppKeys, NwkSKeys and AppSKeys. These keys should normally be replaced when a device is deployed, but that may not always happen. In other cases, AppKeys may not be sufficiently strong, making it easy for attackers to guess them.
IOActive has also reported finding many internet-exposed LoRaWAN servers that use default or weak credentials, making it easy for attackers to access these servers and obtain the keys. Servers can also run software with known vulnerabilities or they may not be configured properly, which also allows attackers to obtain the keys.
Keys can also be obtained by breaching the networks of device manufacturers, hacking the devices used by technicians to configure LoRaWAN systems, and breaching service providers.
Once they have obtained the keys, attackers can launch denial-of-service (DoS) attacks against devices and the network server. Malicious actors could also send fake data to the network, which could have serious consequences.
“Imagine a LoRaWAN device measuring the pressure of a critical gas pipeline, which needs to be under constant monitoring. An attacker with valid session keys could craft and send LoRaWAN messages with normal behavior data for the pipeline pressure, masking any anomaly and hiding a physical attack against this pipeline. If not caught in time, such an attack could lead to an environmental, economic, or, in a worst-case scenario, lethal disaster,” IOActive said in its report.
Another attack scenario described by the security firm targets the smart meters used by utilities. A DoS attack on smart meters will prevent the utility from billing customers, which could have a significant financial impact on a company. In the case of smart cities, targeting street lighting and public transportation signs could cause serious problems. If hackers target a smart home, they may be able to disable alarm systems, unlock doors, and remotely monitor the house.
“The attack scenarios for LoRaWAN networks are nearly endless, these are just a small sample. Each attack scenario will have a different effect, some more dangerous and some less, but each with a real impact on organizations, businesses, and people,” IOActive said.

