Microsoft has decided to remove a couple of Windows security updates that address a UEFI issue after some users complained that the updates caused serious problems.
Some users reported that their devices became unusable after trying to install the KB4524244 security update for Windows 10. Microsoft launched an investigation and decided to pull KB4524244, along with KB4502496, which contains the same patches for Windows 8.1, Windows Server 2012, and an earlier version of Windows 10.
“This standalone security update has been removed due to an issue affecting a sub-set of devices. It will not be re-offered from Windows Update, Windows Server Update Services (WSUS) or Microsoft Update Catalog,” Microsoft said. “Removal of this standalone security update does not affect successful installation or any changes within any other February 11, 2020 security updates, including Latest Cumulative Update (LCU), Monthly Rollup or Security Only update.”
The company has provided workarounds that should help users resolve the problems caused by KB4502496 and KB4524244.
According to Microsoft, the updates address “an issue in which a third-party Unified Extensible Firmware Interface (UEFI) boot manager might expose UEFI-enabled computers to a security vulnerability.”
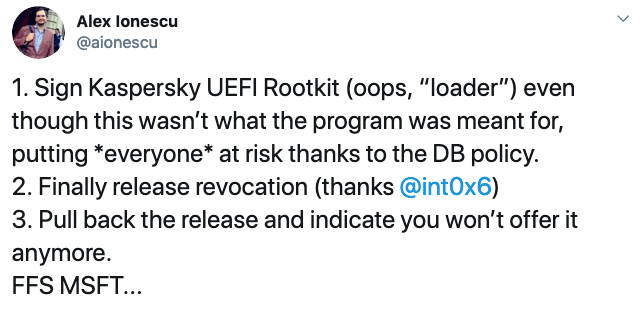
Experts believe the third-party UEFI boot manager referenced by Microsoft is one made by Kaspersky.
In April 2019, a researcher demonstrated how attackers could exploit bootloaders signed by Microsoft to bypass the UEFI Secure Boot feature, which should prevent the execution of unsigned or untrusted code at boot (e.g. bootkits).
The researcher who discovered the method demonstrated his findings by abusing a loader associated with Kaspersky Rescue Disk 2018, which the cybersecurity firm describes as “a free bootable disk for detecting and eliminating threats that interfere with the work of the operating system.”
At the time, the researcher assumed that Microsoft would revoke the certificate used to sign the Kaspersky bootloader to prevent abuse, and it seems that updates KB4502496 and KB4524244 did just that. However, the updates have now been removed and some experts are baffled by Microsoft’s statement that it will not re-release the updates.
UPDATE. Kaspersky has published an FAQ for this issue and clarified that the Rescue Disk vulnerability identified in April 2019 was patched in August. Until a fix was released, the company’s endpoint security products were able to detect exploitation attempts.
The cybersecurity firm pointed out that exploitation of the vulnerability required physical access to the targeted device.
Kaspersky highlighted that a different document from Microsoft states that the company is working on a new version of the buggy update. Kaspersky said an internal analysis determined that the problems with KB4524244 were not caused by its products.
Related: Symantec Endpoint Protection Update Causes Many Devices to Crash
Related: Users Unable to Log on to Windows Due to McAfee Update












