Microsoft on Tuesday released new guidance to help customers defend against credential theft stemming from Pass-the-Hash (PtH) attacks.
In a new white paper called Mitigating Pass-the-Hash and Other Credential Theft, version 2, Microsoft encourages IT professionals to “assume breach” to highlight the need for the use of holistic planning strategies and features in Microsoft Windows to become more resilient against credential theft attacks.
Microsoft describes Pass-the-Hash attacks as a technique in which an attacker captures account logon credentials on one computer and then uses those captured credentials to authenticate other computers over the network.
This latest 60-page report is a follow-up to a previously released report from Microsoft on guidance and mitigations for Pass-the-Hash attacks.
“Given that organizations must continue to operate after a breach, it is critical for them to have a plan to minimize the impact of successful attacks on their ongoing operations,” Matt Thomlinson, Vice President, Microsoft Security, wrote in a blog post. “Adopting an approach that assumes a breach will occur, ensures that organizations have a holistic plan in place before an attack occurs.”
According to Thomlinson, there are three important points technology leaders should understand about a PtH attack:
• First, an attacker has to get a foothold on your network before a PtH type of attack occurs. This is commonly achieved using tactics such as phishing, taking advantage of weak passwords, or by exploiting unpatched vulnerabilities.
• Second, once initial administrative rights to a compromised computer are obtained, an attacker captures account login credentials on that computer, and then uses those captured credentials to authenticate to other computers on the network.
• Third, the ultimate goal of an attacker might be to compromise the domain controller – the central point of control for all computers, corporate identities and credentials – which effectively gives them control and full access to all of the organization’s IT assets.
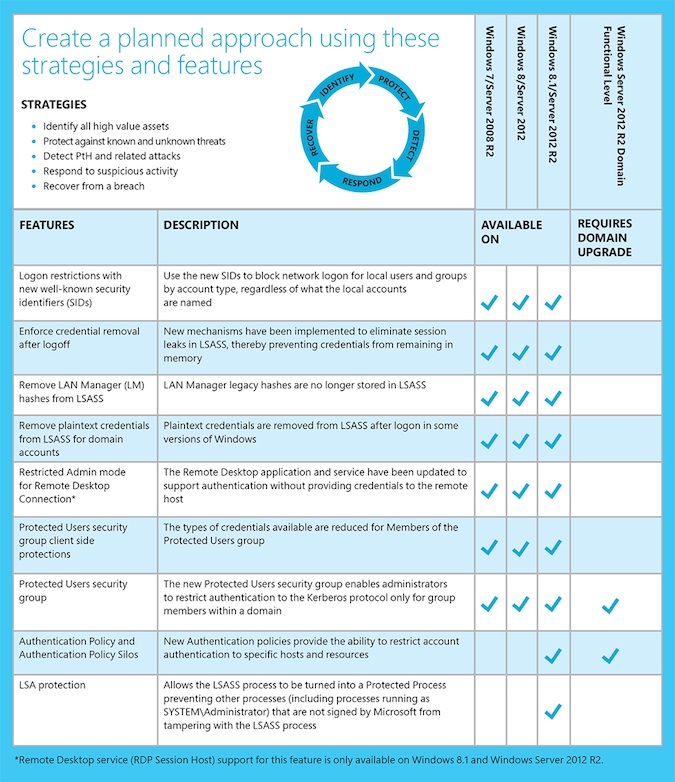
“A planned approach enables defenders to close the seams that attackers are aiming to exploit,” Thomlinson explained. “The guidance also underscores another important point – that technical features alone may not prevent lateral movement and privilege escalation. In order to substantially reduce credential theft attacks, organizations should consider the attacker mindset and use strategies such as identifying key assets, implementing detection mechanisms, and having a breach recovery plan.”
Microsoft provided a list strategies and advice that can be implemented in combination with Windows features to provide a more effective defensive approach, and are also aligned to the National Institute of Standards and Technology (NIST) Cybersecurity Framework.
“Determined adversaries will adapt to the defenses of targeted organizations and seek out new ways of exploiting systems and the people who operate and maintain them,” the report concludes. “It is crucial to recognize that a comprehensive defense approach is needed and that organizations should be prepared to defend against these threats.”

